Report Published November 12, 2020 · 111 minute read
A Roadmap to Strengthen US Cyber Enforcement: Where Do We Go From Here?

The following report is the result of a multiyear effort to define concrete steps to improve the US government’s ability to tackle the scourge of cybercrime by better identifying perpetrators and imposing meaningful consequences on them and those behind their actions. A more complete PDF version of this report, including further information about those involved in its development, can be found here.

Part 1: The Case
The United States faces an unrelenting cybercrime wave that affects nearly every sector of the American economy and threatens US security. As more Americans rely on the Internet and the COVID-19 pandemic causes computer use patterns to change, opportunities grow for cybercrime perpetrators.1Much of America’s debate about cybersecurity policy focuses on defending the country from cyberattacks. However, an existing and growing enforcement gap permits perpetrators of cybercrime targeting American people, companies, and governments to face little to no consequences for their actions. Public opinion research makes clear that American people want more aggressive action from US policymakers to combat cybercrime and punish the culprits. This will require a robust approach that strengthens tools for law enforcement and international diplomacy responses.
The start of a new presidential term in 2021 is an opportunity for the US government to take stock of the myriad challenges that have stymied progress in the global enforcement of cybercrime and to design a strategy to finally address them. In partnership with a bipartisan group of former high-level government officials, experts, and private sector representatives, Third Way launched a project to assess these challenges and propose a cyber enforcement roadmap for the presidential administration in 2021. Our goal is to help the next presidential administration develop a comprehensive cyber enforcement strategy to reduce cybercrime and minimize its impact on the American people by identifying the perpetrators and imposing meaningful consequences on them.
Part 1 of this paper provides an assessment of the current cybercrime problem and impediments to progress. Part 2 proposes a roadmap with detailed, actionable policy recommendations for a new and comprehensive approach to US cyber enforcement that the White House can launch in January 2021 and implement over the next two years.
America’s cybercrime wave and persistent enforcement gap.
The United States is in the midst of a long cybercrime wave targeting America’s people, governments, businesses, and organizations, with no end in sight. Ransomware (a form of cybercrime) has taken entire state and local governments offline, costing millions in recovery costs.2Senior citizens have lost millions of dollars to cybercriminals.3And nation-states are turning to cybercrime to steal America’s closely guarded national security secrets and intellectual property (IP).4
The COVID-19 pandemic has exposed even more opportunities and vulnerabilities. In April, one month into the pandemic, the Federal Bureau of Investigation (FBI) saw an uptick in daily cybercrime reports of more than 400% compared to their typical complaint rates.5Two months later, a top US Secret Service (USSS) official estimated that cybercriminals would steal and scam Americans out of $30 billion in stimulus funds.6Cybercriminals directly targeted the healthcare sector at a time when it faced unprecedented strain due to the pandemic, extorting hospitals and demanding ransom payments to unlock critical data that could keep people alive.7In one such case, the impact of a ransomware incident is suspected to have led to the death of a patient in Germany.8The World Health Organization also reported a five-fold increase of malicious cyber incidents since the outbreak of COVID-19.9
Even before the pandemic, one in four American households had been victimized by cybercrime, making it the most prevalent crime in the United States.10Key data points include:
- The financial impact of ransomware alone increased 1400% between 2015 to 2017.11
- Phishing emails grew over 40% between 2017 and 2018, and the healthcare sector saw a 473% increase of email fraud from 2016 to 2018.12
- A 2018 White House Council of Economic Advisors report estimated that malicious cyber activity cost the US economy anywhere from $57 billion to $109 billion in 2016, and that the price tag would continue to rise.13
- In the private sector, the professional services firm Accenture found that the average cost of cybercrime for companies increased by 12 percent between 2017 and 2018, from $11.7 million to a new high of $13 million.14
A wide range of actors have taken up cybercrime to advance their varied objectives, including state-sponsored or -enabled actors, organized criminal groups, and lone actors. Some US assessments indicate organized criminals and lone cybercriminals are generally motivated by financial reasons, while nation-state actors tend to be more focused on stealing, destroying, or compromising victim data.15The line between nation-state actors and non-state cybercriminals is blurring as states abet and directly employ non-state cybercriminals and/or their tools.16For example, in July 2020, the Department of Justice (DOJ) indicted two criminals contracted by the Chinese government to steal COVID-19 vaccine IP, who also hacked companies for personal financial gain.17This blurring line between state and non-state actors has complicated the ability of governments like the United States to identify the perpetrators of cybercrime and hold them fully accountable.
The current cyber enforcement gap in the United States means cybercriminals largely operate with impunity, rarely facing consequences for victimizing America’s people and institutions.
The widespread use of technology and the growing rates of internet connectivity around the globe, coupled with the continued development of technologies that allow for anonymity on the Internet, have made cybercrime a low-risk, high-yield venture. Unfortunately, law enforcement in the United States and globally has struggled to keep pace. In the United States alone, Third Way found that only 3 in 1,000 cyber incidents reported to the FBI lead to an arrest.18The real gap between incidents and arrests is likely even higher, as victims often do not report cybercrimes.19Available global data indicates that the enforcement gap is no better in many countries where the United States needs support to combat this transnational threat.20
The current cyber enforcement gap in the United States means cybercriminals largely operate with impunity, rarely facing consequences for victimizing America’s people and institutions. The American people want this to change.
Americans want to see the cyber enforcement gap reduced.
An August 2019 poll of 1,685 likely US primary voters found that 92% of respondents said it was important for the next US President to make reducing cybercrime a top priority.21In a 2018 Statista poll, 72% of respondents worried that hackers would steal their personal, credit card, or financial information, placing this concern highest among a list of thirteen crimes.22 Further, a 2019 Chicago Council on Global Affairs survey found that a majority of the 2,000 respondents polled rated cyberattacks on the United States as a top national security threat, mirroring findings in an April 2020 Pew Research Center poll.23
When it comes to bringing cybercriminals to justice, voters believe the federal government is the most important actor. According to a Third Way and Global Strategy Group survey conducted in early 2020 among 2,000 likely voters, 60% believe it is the federal government’s responsibility to investigate and prosecute cybercrime.24
The presidential administration must prioritize reducing this gap in 2021, something that will require a mindset shift and a rebalance of US cybersecurity policies.
Solving the cyber enforcement gap requires a fundamental rebalance in US cybersecurity policies from a heavy focus on building better cyber defenses against intrusion to waging an equally aggressive effort to identify and punish the people behind cyberattacks. This will mean shifting from a cybersecurity approach that often blames the victims to one that puts catching hackers at the forefront.25An approach that emphasizes apprehending criminals and balances international diplomacy with other US capabilities in cyberspace would benefit both the American government and people.
There are many types of cybercriminals, and many types of cybercrimes. The response required by the US government will depend on the specific circumstances of each specific case. To date, however, the US government has over-emphasized and -resourced military responses to secure cyberspace from nation-state actors and impose consequences on them, while America’s domestic law enforcement has not received the level of resources, training, and focus necessary to sufficiently identify, deter, and punish offenders, particularly non-state actors. Further, a militarized, national security approach provides little to no transparency for the American public to understand the country’s own cyber operations, which are often hidden in classified programs.26Additionally, if other countries think a militarized response to malicious cyber activity is the acceptable norm and respond in kind, there is a risk of future military cyber escalation.27Finally, an approach that overemphasizes defensive, militarized action may inadvertently cause policymakers to overlook malicious cyberattacks for private, financial gain and instead focus largely on attacks against US critical infrastructure, despite billions lost annually to ubiquitous cybercrime.28
American policymakers must also change another held mindset if they want to tackle the enforcement gap: they must stop believing that an effort to attribute attacks and punish those responsible is futile. In the past, critics have argued that enforcement actions do not deter future cyberattacks, particularly when it comes to criminals and state-sponsored or -sanctioned actors in the hardest to reach places. Research shows, however, that indictments and prosecutions play an important role in demonstrating the US government’s ability to identify perpetrators, signaling the government’s desire to obtain justice for victims and providing a foundation for government actions to deter future attacks, such as sanctions and diplomatic engagement.29When indictments and prosecutions are deployed strategically, they can be a critical component of broader efforts to punish the perpetrators of cybercrime and reduce its impact on all Americans. A comprehensive approach to combating malicious cyber activity and blunting its consequences would prioritize enforcement actions as one, but not the only, tool in America’s toolbox against this activity. Depending on the perpetrator and activity, the government’s response can include sanctions, asset forfeiture, and diplomatic efforts, as well as military and intelligence options when appropriate and legal.
In sum, cybercrime cannot be combated solely by brute military force or defensive efforts. Instead, the White House in 2021 must provide America’s law enforcement and diplomats with the resources, capabilities, and knowledge needed to identify, stop, and bring to justice perpetrators of cybercrime.
The reasons behind the cyber enforcement gap require dedicated attention.
No single entity is solely responsible for cyber enforcement or addressing the challenges it raises. Cybercrime is difficult to track. The criminals often reside outside of the United States—some in countries either unwilling or unable to cooperate with the US government. Cyber enforcement requires a multitude of partners working seamlessly together across multiple domestic and international jurisdictions. But difficult is not the same as impossible. Accepting futility is not an option. The cybercrime threat is too pervasive and important to lack a dedicated, comprehensive approach for combating it.
Third Way convened nearly 40 experts to identify several large-scale bureaucratic, operational, and (geo)political challenges the United States must address to boost this cyber enforcement. They identified the following challenges:
- First, the White House lacks an empowered, senior cybersecurity advisor who can effectively coordinate federal efforts, promote information sharing, identify and fill intelligence gaps, and create a comprehensive cybercrime strategy. Cybercrime intersects cybersecurity, law enforcement, national security, and foreign policy agendas and therefore requires the engagement of many diverse government entities with varying missions, resources, expertise, and legal authority. While the role of a cybersecurity advisor who acts as a principal advisor to the President and to coordinate federal efforts has existed since the Clinton Administration, it has fluctuated in importance and responsibility. The position was effectively eliminated in 2018.30This hampers the government’s ability to coordinate across the numerous federal entities who play critical roles in combating cybercrime and responding to domestic and international policy issues, such as data privacy, that could have unintended impacts on cyber enforcement.31Without high-level leadership communicating, coordinating, and deconflicting among these entities, federal cybercrime efforts become muddled.
The lack of a senior cybersecurity advisor also hinders the government’s ability to draw upon numerous categories of information, data, and intelligence held by different agencies to create a comprehensive picture of the cybercrime threat that can inform strategies to combat it and blunt its impact. Private and public sector entities have access to a wealth of cybercrime information and intelligence that is shared with the federal government, but the government’s ability to effectively disseminating it to the right entities in a timely manner is the exception rather than the rule. The federal government must formalize a clear and consistent information sharing throughput that improves the timeliness and relevance of information while also addressing legal, cultural, and technological issues. For instance, while national security officials have taken steps to make the Vulnerability Equity Process (VEP) more transparent—the process in which the US government decides to publicly disclose or restrict a vulnerability— a senior cybersecurity advisor is needed to instill greater public confidence and collaboration in the VEP.32And a senior cybersecurity advisor can also work with the Intelligence Community (IC) to advance further assessments on the nature of the cybercrime threat. For well-founded reasons related to protecting privacy and civil liberties, the IC’s primary mission is internationally focused and often unaligned with domestic law enforcement priorities. This dynamic, however, often results in delays in actionable information reaching the public and private entities tasked with dealing with the threat of cybercrime. Better aligning and formalizing cooperation with the IC represents a considerable challenge for these entities and a senior cybersecurity advisor can help address these issues.

- Second, law enforcement cannot accurately measure the cyber enforcement gap and assess progress, because the federal government lacks comprehensive data on how often cybercrime occurs. Currently, fewer than one in ten victims of cybercrime report the crime to law enforcement, in part due to uncertainty about which agency to report to.33Victims may also see no utility in reporting a crime to law enforcement because they rarely receive updates on the status of their report and lack assistance dealing with the financial loss and mental health consequences stemming from the crime. Private sector companies, too, hesitate to report cybercrime to law enforcement due to potential regulatory consequences and loss in profits.34And when crimes are reported to federal and state, local, tribal, and territorial (SLTT) law enforcement, there are various federal databases that they could be entered into, but these databases are neither interoperable nor collected into a central repository.35As a result, the federal government lacks a comprehensive picture on how often cybercrime occurs. This causes policymakers to deprioritize it compared to other crimes and makes it impossible to establish useful metrics to reduce cybercrime or to provide resources commensurate with the threat.
- Third, the federal government does not provide law enforcement personnel with the technical capabilities to analyze digital evidence or the training opportunities needed to expand and diversify the workforce. Over half of local law enforcement agencies do not have access to the resources they need to process digital evidence, even though nearly every crime now produces some digital footprint.36These agencies rely heavily on federal crime labs to assist them in digital forensics, but these labs tend to be inaccessible to rural law enforcement agencies.37Compounding this challenge is the technical competencies SLTT criminal justice personnel need to perform digital forensics analysis to conduct cybercrime investigations.38Recruiting new individuals with these skill sets is exceedingly difficult, with nearly 3,000 public sector jobs for analysts and investigative positions going unfilled.39At the same time, programs to recruit and train federal and SLTT personnel on skills related to digital evidence forensics have been defunded or seen their funding levels remain stagnant despite the rise in cybercrime.40For example, the budget for the FBI’s National Domestic Communications Assistance Center (NDCAC), which offers various technical and training assistance to SLTT on digital evidence, was projected to decrease by 25% with expected funding cuts over the past eight years while the FBI’s total budget has increased roughly 16% during that same period.41
Further, women, minorities, and other underrepresented groups are not adequately recruited, as Black and LatinX employees make up less than 20% of the FBI workforce and women make up only a third of the Department of Homeland Security’s (DHS) workforce.42 Research demonstrates that diverse workforces produce better outcomes and more informed decision-making.43Public agencies also struggle to retain trained employees who are lured away to the private sector to receive higher salaries.44Due to the skills and training gap, the 18,000 SLTT law enforcement agencies in the United States need more robust partnerships with the federal and private partners to make progress, while expanding diversity, equity, and inclusion initiatives. Addressing these training and workforce gaps will likely require increased federal spending. However, the Government Accountability Office (GAO) reported this year that the White House lacked insight into how much agencies should be spending to implement the 2018 National Cyber Strategy, which includes cybercrime goals and commitments on training.45
- Fourth, perpetrators of cybercrime are often located in countries unwilling or unable to cooperate with US diplomats and law enforcement in a timely manner. The US international engagement architecture is not set up at the level needed, nor operated at the efficiency required, to overcome these challenges. A single cybercrime incident can hit victims in multiple countries independent of the location of the perpetrators, which means cybercrime investigations frequently involve criminal justice systems that may, in some cases, lack capacity, tools, and/or harmonized legal regimes. Extradition can be complicated and lengthy. While the US government has provided foreign assistance to governments and international organizations to build capacity on cybercrime, it has largely underinvested in these efforts in comparison to capacity building to combat other security threats. Further, the entirety of this foreign capacity building assistance is extremely difficult to track.46No mechanism exists to assess, monitor, and evaluate these security assistance efforts to determine whether they are achieving objectives and including adequate human rights safeguards to prevent against misuse. This is critically important, as many governments around the globe have used cyber enforcement tools and capabilities to perpetrate human rights abuses and undermine the rule of law.47
For governments that are systematically unwilling to cooperate with the United States, the challenges vary widely depending on the nature of the nation-state and the motivations of the cybercriminal(s). Some governments have “passive” relationships with cybercriminals. They may criminalize such activity but are unable to stop attacks for many reasons, including corruption. In these cases, capacity building and other forms of direct support may be critical. However, some governments ignore or abet malicious cyber activity or directly order or execute attacks themselves, at times employing non-state cybercriminal proxies. Other diplomatic, law enforcement, economic, military, intelligence, or offensive cyber activities may be necessary to incentivize or compel a change in behavior.48
The US government has prioritized the establishment and strengthening of norms guiding responsible state behavior in cyberspace to address the actions of America’s adversaries. Yet the US government has not always been in lockstep with its allies in the development of such norms.49Advancing accountability and enforcement of cyber norms must continue to be a core objective of US cyber diplomacy. And for them to have widespread impact, the United States must be willing to abide by such norms—something it has not always been willing to do. The development of global cyber norms for nation-states must go hand-in-hand with efforts to identify, stop, and bring to justice cybercriminals. This includes the strong promotion of membership to the only legally binding global cybercrime treaty known as the Budapest Convention in order to facilitate cross-border cooperation in these cases.50These two priorities must be pursued in a complementary and reinforcing manner, with the US government leveraging debates on global cyber norms to remind governments of their responsibilities to identify and prosecute cybercriminals.
Unfortunately, the US government currently lacks the robust international engagement architecture to overcome these global challenges. US efforts to impose consequences on countries for malicious cyber activity are hindered by a weakened American diplomatic corps.51The US government needs high-level cyber diplomacy leadership with the resources and personnel to support their efforts, including a US cyber ambassador position and office at the Department of State (DOS). Even with such an office, there will be challenges around deconflicting its role in relation to other government departments and agencies that engage internationally on these issues.
Additionally, America’s retreat from the global stage and multilateral engagement will continue to hinder progress on cyber enforcement. Combating the cybercrime threat requires prioritization at the highest levels of the US government and the expert personnel and resources to advance global engagement—two things that have been inadequate under past administrations. Reasserting US leadership globally on cybercrime and cyber issues more broadly and strengthening multilateral engagement must be a top priority. It will be particularly critical as the presidential administration grapples with if and how the US government will engage in negotiations on a new global cybercrime treaty pushed by Russia. And it will be vital as the US government and other supporters of an open, free, and secure Internet engage in an ongoing global competition with governments who support a more authoritarian model of Internet control on debates around cybersecurity and technology policy more broadly.52The next administration will need to rebuild and reorient the US international engagement architecture to strengthen US global leadership on information and communication technologies (ICT) issues and promote a strong commitment to an open, free, and secure Internet.
- Fifth, and lastly, the current mechanisms the US government uses to share and request cross-border data remain too slow and cumbersome to make substantial progress on cyber enforcement. The US government needs robust partnerships with other countries and the private sector to help investigate, arrest, prosecute, and, when warranted, extradite cybercriminals operating outside US jurisdiction. But the burdensome process for foreign governments to request cross-border data sharing disincentivizes such cooperation and slows investigations. Attempts in recent years to overcome these challenges, including the passage of the Clarifying Lawful Overseas Use of Data (CLOUD) Act, may have an impact, but they will only be applicable to a limited number of governments.53Efforts by certain governments to force data to be stored locally will only serve to further restrict these cross-border data flows.
Reasserting US leadership globally on cybercrime and cyber issues more broadly and strengthening multilateral engagement must be a top priority.
A New Approach to Cyber Enforcement.
From April to October 2020, Third Way convened three bipartisan working groups of former high-level officials from Democratic and Republican administrations, state and local governments, private sector representatives, experts, and academics to create detailed, in-depth policy recommendations on cyber enforcement for the Administration in 2021. These consensus recommendations provide a roadmap toward a comprehensive cyber enforcement strategy that reduces cybercrime by increasing the rate at which global perpetrators are identified and brought to justice.
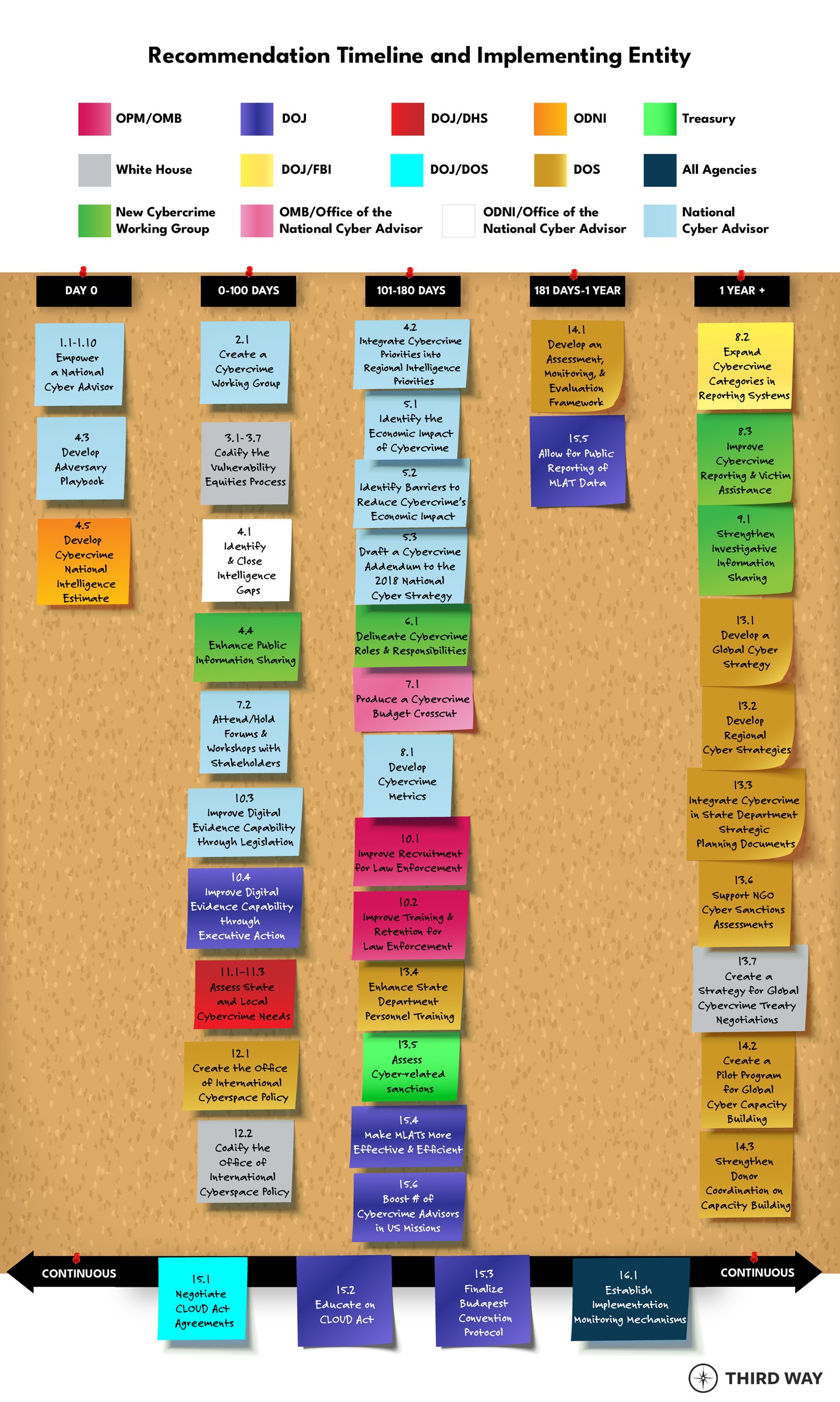
Some recommendations are for the first 100 days of the Administration; others concern new institutions, mechanisms, and assessments to be introduced within the first two years to achieve whole-scale government reforms.
The working groups were organized around three topics:
- White House cybercrime architecture, with a focus on how the next Administration should unify cybercrime policy across the federal government, improve engagement with the private sector, and pave a strategic way forward for cyber enforcement efforts;
- Law enforcement personnel and capacity, with a focus on how federal and SLTT criminal justice agencies can better receive, investigate, and respond to cybercrime, as well as arrest and prosecute criminals; and
- Global cybercrime cooperation, with a focus on how the US government can better cooperate with and support foreign governments’ efforts to impose consequences on perpetrators of cybercrime.
Part 2 of this paper establishes the following objectives for the presidential administration in 2021:
WHITE HOUSE CYBER ENFORCEMENT ARCHITECTURE
Objective 1: Create and empower a National Cyber Advisor position within the Executive Office of the President.54
Objective 2: Enable the Office of the National Cyber Advisor to coordinate with federal agencies to identify, resolve, and develop proposals to improve interagency processes and federal partnerships with external stakeholders to close the cyber enforcement gap.
Objective 3: Introduce legislation that permanently places the VEP under the purview of the Office of the National Cyber Advisor and increases the transparency of the VEP.
Objective 4: Update the US government’s approach to cyber threat intelligence collection and sharing around cybercrime.
Objective 5: Develop a dedicated strategic approach to cyber enforcement as part of a US national cyber strategy.
LAW ENFORCEMENT PERSONNEL AND CAPACITY
Objective 6: Identify and clarify roles and responsibilities for cybercrime investigations among federal and SLTT entities to strengthen institutionalized processes and relationships with public, private, and international partners.
Objective 7: Increase prioritization of cybercrime among federal, SLTT, and private sector stakeholders and direct federal resources to federal and SLTT agencies that are commensurate with its prevalence and impact.
Objective 8: Develop uniform metrics to inform and improve data reporting, victim response, and national data collection mechanisms for federal and SLTT law enforcement.
Objective 9: Strengthen federal and SLTT law enforcement’s ability to share investigative information related to cybercrime.
Objective 10: Improve the digital evidence forensic capacity and capability of federal and SLTT criminal justice agencies by reforming recruitment, training, and retention practices.
Objective 11: Assess the needs, resources, and capacity of SLTT criminal justice agencies and federal-state collaborative organizations to address cybercrime.
GLOBAL CYBERCRIME COOPERATION
Objective 12: Establish a new DOS structure to ensure a well-resourced single point of high-level leadership for all cyber diplomacy matters, backed by an architecture that allows for other bureaus advancing policy and programming on cybercrime to effectively coordinate.
Objective 13: Identify a set of diplomatic tools and policy options to boost international cooperation in cybercrime investigations and address governments that are systematically uncooperative.
Objective 14: Identify a group of countries where the US government is not receiving timely assistance in cybercrime investigations and develop programs to support their criminal justice capacity building needs—including operational support, policy development, and harmonization of laws—to boost cooperation.
Objective 15: Streamline the process and improve the timeline for responding to cross-border data requests, in accordance with substantive and procedural protections.
MONITORING AND MEASURING IMPLEMENTATION
Objective 16: Establish processes at lead agencies to measure the implementation of all objectives.
While the objectives above have implications for US policy on a broad range of cyber-related issues, the recommendations to implement them are organized around a unified goal: imposing consequences on the perpetrators of cybercrime and providing justice to their victims in order to reduce the damage cybercrime is causing in America. Americans of all stripes are being victimized daily by cybercrime, and US policymakers must take decisive action to answer this threat. Jurisdictional and geopolitical challenges, insufficient resources, and a lack of an organized government architecture can no longer justify a US cybersecurity strategy that fails to prioritize cyber enforcement. It is critical that the United States have its own cyber enforcement house in order as it competes on the global stage with countries like China and Russia on issues and standards around cybersecurity and technology policy more broadly. It is time for the United States to close the cyber enforcement gap.
Part 2: The Roadmap
Presidential administrations have undertaken important efforts to bring perpetrators of cybercrime to justice. But the rising cybercrime wave and yawning cyber enforcement gap makes clear that these are not enough. Today, cybercriminals largely operate with impunity. And the people working on these issues day and night need, and deserve, more support from the highest levels of the US government. Change must start with a presidential administration in 2021 that puts cybercrime at the forefront of America’s cybersecurity agenda and commits the US government to a new, comprehensive approach to cyber enforcement.
The policy recommendations below are from the three bipartisan working groups Third Way convened to develop a roadmap on cyber enforcement. Some actions are for the first 100 days of a presidential administration; others will take longer. Many will affect a wide range of cyber-related challenges the US government is facing.
Recommendations are grouped around three themes: The White House Cyber Enforcement Architecture, Law Enforcement Personnel and Capacity, and Global Cybercrime Cooperation. Many recommendations are complementary and, at times, contingent upon each other. Implementation timelines are noted in parenthesis after each.55The working groups tried to identify and prioritize those recommendations that make structural changes within the US government and that create assessments needed to inform and implement policies and strategies for cyber enforcement in the longer term.
White House Cyber Enforcement Architecture
Objective 1: Create and empower a National Cyber Advisor (NCA) position within the Executive Office of the President (EOP).
1.1 The NCA should be located within the EOP (Day 0).
With the 2018 removal of the White House Cybersecurity Coordinator, the President lacks a principal, senior staff advisor on cyber policy. This removal signaled to many that the United States deprioritized cybersecurity. It must be reversed. The NCA should be located within the EOP to advise the President directly. The President should install the NCA as their principal advisor and coordinator on cyber issues and ensure that the position is staffed and empowered to perform this role effectively. The NCA should be a staff position with a role similar to that of the National Security Advisor, Homeland Security Advisor, and National Economic Advisor. The President should create this position as part of their presidential directive to establish the administration’s National Security Council (NSC).
Once appointed, the NCA should work across agencies to develop a domestic and international engagement plan on cybercrime. This should include identifying opportunities to demonstrate presidential-level commitment to this issue globally, such as making it a component of the President’s speech at the United Nations (UN) General Assembly or during the 10-year anniversary of the opening of the Budapest Convention in November 2021.
1.2 The NCA should be an NSC deputy (Day 0).
Because cyber issues are critical and intersect with other NSC constituents, the NCA should serve on the NSC Deputies Committee. The NCA should be invited to all NSC meetings that address cybersecurity, and NSC staff should be involved when NCA efforts affect national security. The National Security Advisor, the NCA, and their staffs should collaborate closely on cybersecurity matters and maintain frequent, open communication.
1.3 The NCA should not require Senate confirmation (Day 0).
The NCA would best fulfill their cybersecurity responsibilities as a presidential advisor integrated into the NSC staff, so the position should not be subject to Senate confirmation. Other similarly situated presidential advisors are not Senate confirmed, because to do so would interfere with the President’s ability to choose and interact with their closest staff advisors. Like other senior presidential advisors, the principal roles of the NCA are to advise the President and develop and coordinate policy. Unlike Senate-confirmed officers, the NCA would not have operational authorities. A requirement of Senate confirmation—and the significant obligations for congressional testimony that come with it—would unnecessarily create distance from the President and undermine the trust and responsiveness that makes similar advisor roles so effective. Simply put, Senate confirmation of the NCA would diminish the President’s ability to rely on the position.
1.4 The NCA should be supported by an Office of the National Cyber Advisor (ONCA) (Day 0).
The NCA should have the assistance of a well-staffed Office of the National Cyber Advisor (ONCA). Currently, no single office coordinates the overlapping responsibilities of federal agencies with cybersecurity responsibilities. The NCA needs staff to help manage the vast cyber policy development, coordination, and advisory process. In addition, the office will work with the many federal agencies with cybersecurity responsibilities to resolve conflicting priorities, develop policies and priorities, and provide leadership in resolving disputes between the government and the private sector around cyber policy.56The ONCA should be located outside the NSC because many of its responsibilities do not involve national security and will require frequent interaction with the private sector, which can be difficult inside the NSC.
1.5 The ONCA should play a role in planning, organizing, and overseeing strategic disruption of criminal infrastructure (Day 0).
Cybercrime disruption operations have policy implications and potential sensitivities around the actors involved, both of which require the type of central coordination that the ONCA can provide. Such a role is critical for overseeing strategic disruptions that fracture criminal relationships and ecosystems. The ONCA should help coordinate cyber operations that are both proactive and responsive. The NCA should orchestrate this coordination by using the NSC interagency process to prioritize and set the parameters for disruption operations and determine the broad, strategic rules of engagement for systemic disruption campaign activities.
To be clear, the NCA should have no operational authority; rather, the NCA should strictly coordinate and advise on policy. Neither the NCA nor ONCA should direct operations, and operational authority should remain with the agencies currently mandated to carry out such operations so as not to impede established processes or create jurisdictional conflict.
1.6 The ONCA should be allotted a staff of 25-30 people (Day 0).
With specific guidance for each role, 25-30 people would efficiently execute the responsibilities of the ONCA and would allow the Office to maintain effectiveness.57Staffing should center around specific policy challenges as well as the areas of threat response, asset response, and intelligence support as detailed in Presidential Priority Directive 41.58A staff of this size would not have the capacity to develop an independent policy process, so the ONCA should be encouraged to participate in pre-existing interagency policy processes and focus its efforts on advising interagency coordination. This recommendation would quintuple the current NSC cyber staff and would double the highest count of people dedicated to supporting the White House Cybersecurity Coordinator during the Obama Administration.
Staff should largely be composed of employees on rotating details, including details from DOJ and DHS to cover cybercrime issues. These positions should be staffed by personnel from the FBI and USSS. The ONCA should also hire a small number of permanent staff to support the office and maintain institutional knowledge.
This office should also share staff with the NSC, Office of Management and Budget (OMB), National Economic Council (NEC), and the Office of Science and Technology Policy. The former Office of the Cyber Coordinator was most effective when it harmonized its activities with other EOP elements. The US cyber community needs the NCA to provide leadership for the resolution of interagency disputes around cyber issues. Because the ONCA will need an in-depth understanding of the economic incentives involved in cybercrime, a member of the NEC should serve as a deputy in the ONCA.59This role should focus on tackling financial cybercrime and protecting the global financial system from abuse, as outlined in the updated National Cyber Strategy and in line with the recommendations of the ‘International Strategy to Better Protect the Global Financial System Against Cyber Threats (2021-2024)’ developed by the Carnegie Endowment for International Peace in partnership with the World Economic Forum.60As US cybersecurity priorities shift, the number of staff from each of these organizations may vary. To maintain agility, the ONCA should augment its staff with experts from academia, nonprofits, and SLTT governments through the Intergovernmental Personnel Act.61
1.7 The ONCA should have dedicated funding within the EOP budget (Day 0).
The EOP budget should include dedicated funding for the ONCA because an organization of this size must have its own congressional budget approval to work within the EOP. The White House should take a phased approach for funding this Office. For FY 2021, the ONCA should be funded through the White House. The FY 2022 budget should include a separate line item for the Office within the broader EOP budget and should give the ONCA the funding and authority to reimburse agencies for services, personnel, and facilities. The ONCA should also have the authority to hire private sector expertise on an expedited basis (such as through the US Digital Service), and to employ consultants and experts on a per diem basis. The ONCA is expected to cost between $5 million to $6 million annually.
1.8 The ONCA should concurrently review federal cybersecurity budgets with OMB (Day 0).
Part of fulfilling the coordination role for federal cybersecurity includes ensuring that proposed agency budgets are aligned with the administration’s cybersecurity strategy. To do this, federal cybersecurity agencies should submit their budgets to OMB and the ONCA simultaneously. The ONCA should review the proposed agency budgets for consistency with the administration’s cybersecurity strategy. Additionally, the Office should provide its analysis to both OMB and the submitting agency on where spending could be increased or decreased to align with the strategy. When OMB receives reprogramming transfer requests that affect cybersecurity funding, OMB should consult with ONCA. The ONCA should have at least one OMB staffer and one other person who interfaces with the OMB and budget staffers in other offices.
1.9 The ONCA should be transparent about its interaction with the private sector (Day 0).
Given the significant role that the private sector plays in cybersecurity, the ONCA should have the authority and responsibility to meet with representatives from the private sector. Non-NSC members of the ONCA staff should interface with the private sector. As an NSC deputy, the NCA would not meet directly with members of the private sector. In its work with the private sector, the ONCA should look to and support the recommendations and principles of initiatives focused on building public-private partnerships on cybercrime and cybersecurity, including the Carnegie Endowment’s ‘International Strategy to Better Protect the Global Financial System Against Cyber Threats (2021-2024)’ and the World Economic Forum’s Partnership against Cybercrime.62To further avoid the appearance of improper influence, the ONCA should maintain a clear, public record of staff meetings and their participants.
1.10 The ONCA should prioritize transparency by publishing an annual report (Day 0).
The ONCA should produce a yearly report for Congress and the public to foster accountability and public trust. In this report, the ONCA should publish a list of all meeting attendees to track interactions between the private sector and the ONCA, as mentioned above.63This report should also include the unclassified report on the VEP, which will be discussed in the following set of recommendations.
Objective 2: Enable the ONCA to coordinate with federal agencies to identify, resolve, and develop proposals to improve interagency processes and federal partnerships with external stakeholders to close the cyber enforcement gap.
2.1 The ONCA should lead a temporary, intergovernmental Cybercrime Working Group that consists of relevant federal entities to assess and develop interagency cyber enforcement policies and legislative proposals where cross-agency coordination and cooperation is required and to coordinate with the private sector and SLTT partners when necessary (0-100 Days).
Several federal entities have cybercrime missions that overlap, which requires ongoing coordination and cooperation across these entities to resolve legal, strategic, budgetary, and policy disputes and challenges (see figure below). The National Cyber Investigative Joint Task Force (NCIJTF) coordinates interagency operational efforts related to cyber investigations, but no similar body exists to resolve policy disagreements on cyber enforcement, like how to best engage international partners, improve information sharing, and increase incident reporting.

- Enhancing effective intergovernmental and public information sharing about cyber threat vectors (Recommendation 4.4).
- Clearly delineating cyber enforcement roles and responsibilities within federal entities and between federal and state entities to create more effective interagency coordination mechanisms (Recommendation 6.1).
- Developing proposals that improve cybercrime reporting among public and private victims and the assistance awarded to them (Recommendation 8.3).
- Enhancing information sharing mechanisms to improve investigative coordination (Recommendation 9.1).
Once the Cybercrime Working Group fulfills these recommendations, the ONCA should consult with the Working Group’s members to determine if it should be dissolved or remain a standing forum to handle interagency policy disputes.
Objective 3: Introduce legislation that permanently places the VEP under the purview of the ONCA and increases the transparency of the VEP.
3.1 The NCA should work with Congress to develop legislation establishing a permanent Equities Review Board (ERB) within the ONCA (0-100 Days).
The VEP is the process by which the federal government “balances whether to disclose vulnerability information to the vendor with the expectation that they will patch the vulnerability, or temporarily restrict knowledge of the vulnerability so that it can be used for national security or law enforcement purposes.”65The VEP Charter describes the vulnerabilities equities policy and process and provides guidelines for the VEP, including the composition and role of the interagency ERB.66The ERB is the primary forum for interagency deliberation and determination concerning the VEP.67However, despite the importance of having such an interagency forum to make these difficult decisions, the ERB is not legislatively mandated. To remedy this and ensure proper oversight, the NCA should work with Congress to develop legislation creating a permanent ERB within the ONCA.
Permanent members of the ERB should include representatives from the organizations in its charter68 The legislation should enable the NCA to add other permanent members or invite other agencies to attend meetings as needed.69
3.2 In this legislation, Congress should establish a permanent VEP Director position to lead the ERB, supported by an Executive Secretariat (0-100 Days).
The VEP Director’s responsibilities should be transferred from the NSC to a permanent position in the ONCA, which would now have the staff to support the VEP. While the NCA may elect to appoint someone to this position, the NCA could also choose to serve as the VEP Director. The Executive Secretariat, currently staffed by the National Security Agency, should be moved permanently to the ONCA.70This group would retain all responsibilities previously established through the VEP Charter.
3.3 Congress should require all US government agencies to timely submit all known vulnerabilities for review by the ERB (0-100 Days).
Currently, agencies share vulnerabilities with the ERB voluntarily. By requiring agencies to share all known vulnerabilities, the VEP would maximize its ability to protect Americans by giving the government time to get ahead of cyberattacks. This legislation should encourage the NCA and VEP Director (if the NCA chooses a separate person to serve as VEP Director) to collaboratively agree on a deadline by which agencies must submit vulnerabilities upon learning of them.
3.4 Congress should require the VEP Executive Secretariat to publish an annual report about the ERB (0-100 Days).
The VEP Charter from 2017 suggests, but doesn’t require, that the VEP Executive Secretariat publish an annual report about the ERB.71The ERB has never done so.72This lack of transparency promotes skepticism about the process and sows distrust in the VEP’s motives and efficacy. To reverse this trend, the legislation should mandate that the Executive Secretariat publish an annual report.
The report should include an unclassified section, delivered to Congress and published on the NCA’s website, and a classified annex delivered only to the congressional intelligence committees. The unclassified section should contain aggregate information and metrics about the disclosure of vulnerabilities to give the public insight into the VEP and track its long-term effectiveness. This section may include the percentage of vulnerabilities disclosed to operators and manufacturers or the average time from discovery to the determination to disclose vulnerabilities.
The classified annex should include information about the types of vulnerabilities that were found and how they were used. It should identify which specific exploits from individual companies and platforms were disclosed and which were retained. This report should additionally identify which agencies most frequently called for vulnerabilities to be retained. Finally, this report should identify how many vulnerabilities are retained for espionage or law enforcement purposes, and how many vulnerabilities are retained for domestic or international criminal cases.
3.5 The VEP Director should clarify that the VEP applies to both purchased and internally discovered vulnerabilities (0-100 Days).
While the VEP has consistently been used to analyze vulnerabilities discovered by government agencies, it has been less clear on whether this process can be used for vulnerabilities purchased by the government. The VEP Director should publish a statement saying that the VEP will also be used to analyze purchased vulnerabilities. Eliminating gray areas to better define the parameters of the VEP ensures smoother operation and eliminates a source of contention between VEP stakeholders.
3.6 The VEP Director should ensure that voting power within the ERB is distributed equitably and should clarify the process to resolve disagreements (0-100 Days).
The legitimacy and efficacy of the VEP process rests on the notion that all perspectives are considered, and that voting power is fairly apportioned. Ideally, the ERB should try to achieve consensus with every decision to disclose or retain a vulnerability, and voting should be used only when consensus cannot be reached.
However, given the variability of the decision-making process of the VEP across administrations, the VEP Director should examine past votes to analyze and restructure voting within the ERB so that all the right voices are at the table. ERB voting rights should be granted solely to department-level agencies. Each department should have a single voting representative, but that representative may come from a sub-agency within the department. This representative should consult with the relevant sub-agencies before each ERB meeting to collect the agencies’ input about each vulnerability.
The VEP Director should also clarify the decision-making process to disclose vulnerabilities when consensus cannot be reached and voting remains divided. A standardized process can streamline the length of time required to reach a conclusion by setting expectations, providing consistency, and allowing for precedent in decision-making. If no consensus can be reached and voting does not resolve disagreements, the decision to disclose or retain a given vulnerability should be sent to the NCA to call an NSC Deputies Committee meeting. The VEP Director should encourage subject matter experts to attend these meetings to explain the technical nature of cyber vulnerabilities.
3.7 The VEP Director should establish procedures for conducting regular reviews of the ERB (0-100 Days).
The VEP is a relatively new process that addresses a dynamic problem, so the current implementation must be monitored for inefficiencies and gaps. As such, the VEP Director should require the Executive Secretariat to conduct regular internal reviews of the VEP to answer the following questions:
- How often does each agency vote to disclose vulnerabilities?
- How many vulnerabilities has each agency recently submitted?
- What is the average length of the review process?
- Which parts of the review process are taking the longest amount of time?
- How often does the ERB have to ask for additional information before making a decision?
- Where do information gaps most frequently occur?
The VEP Director should also conduct regular reviews with VEP counterparts in other governments to determine which VEP models are the most efficient and effective.
Objective 4: Update the US government’s approach to cyber threat intelligence collection and sharing around cybercrime.
4.1 ODNI and ONCA should create a joint working group to identify intelligence collection gaps on cybercrime and propose ways to close those gaps (0-100 Days).
The IC cyber collection capabilities are enormous, and they appropriately focus them on nation-state actors and the growing threat they pose.73On the other hand, private sector cybersecurity companies collect vast amounts of information on cybercrime, but that information is not always shared with the government. Even if private sector information were shared more systematically, that information alone is likely insufficient to support US government actions, such as arrest and prosecution. Therefore, the White House should establish a joint ODNI and ONCA working group to identify the intelligence gaps related to cybercrime and what sources could be used to fill those gaps. Where possible, the US government should seek private sector, non-profit, and foreign government sources for technical and contextual information, focusing IC assets on the key step of attribution to specific individuals.
4.2 The ONCA should integrate functional intelligence collection priorities related to cybercrime into regional intelligence priorities (101-180 Days).
The National Intelligence Strategy’s topical mission objective of cyber threat intelligence should be better integrated into regional intelligence priorities.74Currently, intelligence resources are primarily aligned against traditional and legacy threats, and they typically do not prioritize or integrate information with cybercrime implications. All intelligence collectors should be trained to identify information that could potentially be related to the broad spectrum of cyber threats, not only high-end nation-states. Analysts looking at trends for specific countries or regions should be trained in cybersecurity terminology so that they can best search for cyber threat vectors. Within the first 100 days, the ONCA should create and disperse a cyber training guide for collectors and analysts covering different regional intelligence priorities.
4.3 The ONCA should work with the IC to update US government cyber threat intelligence analysis to produce adversary playbooks that describe cyber threat actors’ typical tactics, techniques, and procedures (TTPs) (Day 0).
Consistent with the Department of Defense’s “defend forward” approach, intelligence analysts should develop methods to predict where cybercriminals might move next and how their TTPs might evolve.75Taken as a whole, cyber incidents offer valuable insights into threat actors’ operations and TTPs. The US government could use this information to develop “adversary playbooks,” which would describe how different actor groups operate, map their operational steps, and catalog their TTPs. These playbooks would inform network defenders’ priorities and guide the detection of additional malicious activity. Such playbooks could also identify where adversaries would be most vulnerable to long-term disruption and how their TTPs might evolve. The next Administration should encourage the IC to examine how rapidly evolving situations like global pandemics or social movements may shift TTPs. Organizations such as MITRE and companies like Palo Alto Networks are developing adversary playbooks based on private sector information; the IC should augment these playbooks with US government information.76
4.4 The Cybercrime Working Group should enhance effective intergovernmental and public information sharing about cyber threat vectors, including those related to cybercrime (0-100 Days).
Existing mechanisms for the distribution of cyber threat information from the government, like DHS Automated Indicator Sharing, are ineffective because they often provide the wrong information to the wrong constituencies.77This problem may partially stem from the burden on individual, resource-strapped organizations to identify what information to share with outside parties.78Therefore, the US government needs to refine its approach to information sharing and determine which organizations need to receive which type of cyber information. For example, most companies do not need and cannot use technical cyber threat information; instead, they need to know what concrete steps they should take to stop a new type of threat. The Cybercrime Working Group could help by identifying the types of cyber information that would benefit organizations, mechanisms for distributing that information, and opportunities to further declassify information to reach a wider audience. The Working Group should consult with the private sector, non-profit organizations, and related entities to develop this guide for effective information sharing activities.
As part of this effort, the Working Group should also review individual agencies’ public information sharing alerts. Currently, each federal agency is incentivized to release public alerts about cyber threats and vulnerabilities to bolster the agency’s reach and legitimacy.79However, this disaggregated communication often threatens other agencies’ operations and appears disjointed. It disincentivizes members of the public from sharing cyber-threat information with the government because it is unclear which agency should receive information. In fact, DOJ lists eight different entities that span several DOJ and DHS agencies for victims and entities to report to.80The Working Group should develop a proposal to create a mechanism for the public to submit cyber threat information and allow for the distribution of this information to all necessary federal agencies. This proposal should require the ONCA to develop an interagency process to coordinate the publication and analysis of any cyber threat information shared with the public, as well as breaking down barriers that impede interagency information sharing.81
The ONCA should strive to incentivize robust participation in the Working Group. The willingness of government entities to share information is crucial to fostering stronger relationships with the private sector, which owns upwards of 85% of all critical infrastructure in the United States.82Only with agencies’ willingness to fully participate can the federal government work best with the private sector to defend our nation’s critical infrastructure from cybercrime.
4.5 The Director of National Intelligence (DNI) shall prepare a National Intelligence Estimate (NIE) on the relationship between criminal cyber actors and nation-states (Day 0).
Intelligence services of nation-state actors have relied on non-state, criminal actors to acquire and disseminate information, exploits, and funding. For example, in 2016 the Russian GRU, their military intelligence agency, developed a relationship with and relied upon non-state actors like Wikileaks to disseminate emails stolen from the Democratic National Committee and other individuals associated with a US presidential campaign.83As reported to the UN Security Council, North Korea has long pursued efforts to steal money from financial institutions and cryptocurrency exchanges to evade sanctions and has done so in cooperation with cybercriminals, including in Eastern Europe.84Criminals who steal massive databases with personally identifiable information may mine it for financial gain, while nation-state actors mine the same information for phishing attempts against high-value targets.
Intelligence services of nation-state actors have relied on non-state, criminal actors to acquire and disseminate information, exploits, and funding.
This NIE should review the capabilities, scope, activities, and impact of criminal cyber actors to better understand the evolving ecosystem of malicious cyber actors and their relationship to nation-state adversaries. The report shall include the community’s estimate of the number of criminal organizations operating in cyberspace, their geographic distribution, and their relationship to nation-state governments. The DNI shall concurrently release an unclassified version of the NIE.
By identifying the tactics, relationships, and even identities of cybercriminals, the US government can develop an effective strategy to disrupt the ecosystem that feeds malicious cyber activity at the source.85
Objective 5: Develop a dedicated strategic approach to cyber enforcement as part of a US national cyber strategy.
5.1 The NCA should target a specific amount by which to reduce the economic impact of cybercrime by 2024 (101-180 Days).
Ultimately, the success of the NCA and the ONCA in tackling cybercrime will be determined by metrics of measurable impact (see Recommendation 8.1). First and foremost, the NCA should set a goal to reduce the impact of cybercrime on the US economy by a certain percentage by 2024. This number should be both ambitious and attainable. The NCA should select a point person within the ONCA to lead the development of a written strategy (see Recommendation 5.3) to achieve this goal. This person will ensure that the strategy is written by an established deadline and will lead all meetings related to its development.
5.2 ONCA staff should consult the private sector and civil society groups to identify barriers to the reduction of the economic impact of cybercrime (101-180 Days).
The private sector and non-governmental organizations are best positioned to identify the current policy, legislative, and diplomatic barriers to the reduction of the economic impact of cybercrime. The ONCA should meet with information sharing and analysis centers (ISACs) and sector coordinating councils (SCCs) to develop strategies to overcome these barriers.
5.3 The NCA should work through an interagency process to immediately draft a cybercrime addendum to the 2018 National Cyber Strategy and eventually strengthen the cybercrime components of a new or updated national cyber strategy (101-180 Days).
The NCA should work through an interagency process to update or draft a new national cyber strategy, which should occur every four years. This requirement will ensure that each administration strategically adapts to the ever-changing cyber landscape. By updating, instead of drafting a whole new strategy, the NCA can avoid spending time on an extended process, because most elements of the last strategy can and should remain consistent over time.
The 2018 National Cyber Strategy articulates four pillars to promote US cybersecurity, including one objective focused on cybercrime. This graphic details the priority actions of this cybercrime objective and the actors responsible for implementation.
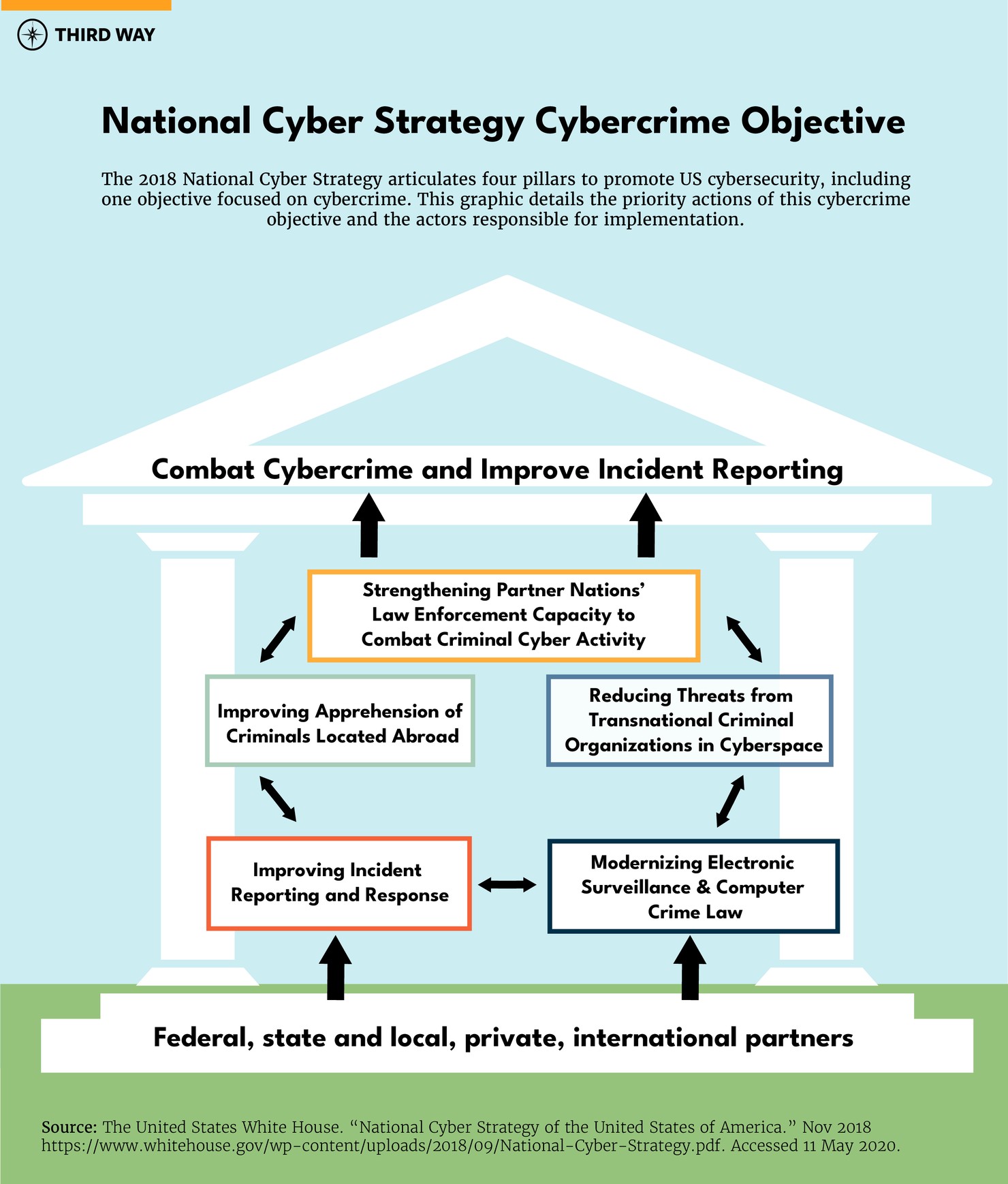
However, due to the time and resources that it will take to develop a national strategy, the NCA should immediately work to draft a public addendum that details how the government will combat the threat of cybercrime to the 2018 National Cyber Strategy in the interim. Pillar 1 of the 2018 National Cyber Strategy aims to “Combat Cybercrime and Improve Incident Reporting,” but is overly broad in how it would achieve objectives, misses critical components of a comprehensive cyber enforcement approach (as outlined in this roadmap), and lacks metrics to evaluate efforts to combat cybercrime.86After consulting with state and private partners through ISACs and SCCs, the ONCA should hold a meeting with representatives from federal agencies with cybercrime responsibilities to analyze the most significant barriers to reducing the economic and national security impacts of cybercrime and identify and implement concrete steps to overcome those barriers (see Recommendations 5.1 and 5.2).
Law Enforcement Personnel and Capacity
Objective 6: Identify and clarify roles and responsibilities for cybercrime investigations among federal and SLTT entities to strengthen institutionalized processes and relationships with public, private, and international partners.
6.1 The Cybercrime Working Group should clearly delineate cyber enforcement roles and responsibilities within federal entities, and between federal and SLTT, private, and international partners, to create more effective interagency coordination (101-180 Days).
At least 20 federal departments and agencies have key roles and responsibilities—which often overlap—in investigating, pursuing, and prosecuting cybercriminals.87Federal policies and laws describe components of these roles and responsibilities, but they do not delineate how these departments and agencies should interact with each other and coordinate where their jurisdictions overlap.88For example, DOS leads much of the US government’s diplomatic engagement on cyber issues, but DOJ and other departments and agencies also develop US global cyber policy and work with foreign partners. Clarified roles and responsibilities in international cyber engagement is just one area where streamlined interagency coordination is required.
More clarity is also needed on federal entities’ roles and responsibilities for coordinating with SLTT and private sector partners. SLTT criminal justice agencies have long partnered with federal agencies on traditional criminal cases, but these partnerships will need to adjust to account for the unique challenges associated with cybercrime. By contrast, the federal government does not have the same historical, routine partnerships with the private sector. With perpetrators of cybercrime abusing private networks and ICT infrastructure, federal law enforcement must develop a framework for when and how they partner with private companies to engage in disruption operations that target criminal infrastructure. While agencies have engaged in disruption operations with companies in the past, such as disrupting domains associated with COVID-19 scams, providing policy and legal clarity on such operations could further strengthen public-private partnerships.89
The Cybercrime Working Group (see Recommendation 2.1) should identify existing cyber enforcement roles and responsibilities within federal entities to improve and, when needed, create new interagency coordination mechanisms. Specifically, the Working Group should:
- Outline current federal departments and agencies' roles, responsibilities, and legal authorities and their associated challenges for receiving, responding, and investigating cybercrimes. This should also include challenges associated with arresting and prosecuting criminals and working with SLTT, foreign, and private partners in pursuing these efforts.90The Working Group should then develop policy and legislative proposals that address these challenges.
- Conduct cost/benefit analyses of previous administration and congressional proposals to reform the US cyber enforcement architecture, such as moving the USSS back to the Treasury Department.91This analysis should also consider possible organizational reforms within DOJ to help cybercrime investigations and prosecutions become more efficient, nimble, standardized, and better coordinated within the Department and across its US Attorney Offices.
- Review, clarify, and/or create appropriate thresholds (with SLTT input) for when the federal government opens an investigation based on a referral from SLTT law enforcement and set policies for how to better support cases emanating from SLTT investigations.92The review process should consider whether regional thresholds need to be established to account for various demographics that exist across regions (e.g., rural vs. urban) and Recommendation 11.1’s assessment.
- Create a uniform definition for cybercrime that the federal government can use for creating policies and informing data collection efforts and incentivize SLTT criminal justice partners to adopt a similar definition.93This definition could then be enumerated in a National Security Presidential Directive (NSPD), similar to NSPD 54, which defined “cyberspace.”94With a definition, the federal government can better create specific policies, implement strategies, and design metrics around cybercrime.95
- Create a framework within which government agencies can assess (with input from private sector partners) ethical, economical, and global equities and determine whether a cybercrime incident is best mitigated through a traditional law enforcement approach, through a disruption operation with private partners, or a combination of the two. This framework should take into account the policies developed in Recommendation 1.5.
Objective 7: Increase prioritization of cybercrime among federal, SLTT, and private sector stakeholders and direct federal resources to federal and SLTT agencies that are commensurate with its prevalence and impact.
7.1 OMB and the ONCA should review all federal departments and agencies with cyber enforcement missions to create a comprehensive cyber enforcement budget proposal for the President’s Budget Request for FY 2023 and/or FY 2024 (101-180 Days).
Federal departments and agencies responsible for cyber enforcement have seen flat or declining cyber enforcement budgets. Relevant entities within DHS, the FBI, and DOS have faced proposed or implemented budget cuts over the past few years, diminishing their capacity to train and engage domestic and foreign partners.96For example, the USSS National Computer Forensics Institute (NCFI), which offers training courses to SLTT personnel, requires $35 million to operate at full capacity, but was proposed to receive $4 million for FY 2021.97
Budget shortfalls at the federal level impact SLTT agencies as well, leading to fewer opportunities to train cybercrime investigators and prosecutors through programs operated by the FBI and USSS.98As a consequence of this lower spending, DOJ and DHS’ grants awarded to nonprofits bear a heavier responsibility to fill the training gap, such as those provided to the National White Collar Crime Center (NW3C).99
With the President’s FY 2022 budget proposal well underway, OMB should consult with the ONCA to create a comprehensive cyber enforcement crosscut for the President’s Budget Request for FY 2023 and/or FY 2024. For federal departments and agencies with cyber enforcement missions, the crosscut should, at the minimum:
- Detail the current resources allocated to the department/agency used for cyber enforcement purposes.
- Identify nonprofits whose work supports federal and SLTT criminal justice agencies and receive federal funding or grants, list the amount and source of federal funding, and identify how much funding is needed to operate at full capacity.100
- Identify existing grants that SLTT criminal justice agencies use for cyber enforcement missions, how much each SLTT entity receives, and how they use those funds for cyber enforcement initiatives (see also Recommendation 11.2).
- Request additional funding to reimburse federal entities for their detailees on interagency task forces. Specifically, DOJ should require the FBI to request additional funding in its proposed budget for FY 2023 to reimburse participating agencies for the detailees they send to the NCIJTF to support their interagency cyber enforcement efforts.
7.2 The ONCA should develop a plan to attend and hold a series of forums and workshops with SLTT and private sector participants to discuss the challenges to cyber enforcement and areas to improve partnerships (0-100 Days).
Since 2015, DOJ has held an annual “Cybercrime Symposium” to discuss cybercrime trends, challenges, and lessons learned with academic, private sector, and government practitioners.101The FBI, DHS’s Homeland Security Investigations, and USSS have also held events with stakeholders to develop partnerships and reinforce the importance of cyber enforcement.102Additionally, the government convenes forums with nonprofit organizations like NW3C, which has brought together senior cybercrime investigators from each state every year since 2003 to discuss cyber enforcement challenges and solutions. Private sector companies, too, host numerous events throughout the year that federal government officials speak at to highlight their respective agencies’ priorities and challenges.
The ONCA should coordinate with relevant federal departments and agencies to organize or participate in events to discuss the administration’s cybercrime priorities and overcome challenges to strengthening partnerships. Departments and agencies that have hosted relevant events in the past should include in their FY 2023 and/or FY 2024 budget requests the costs to operate those events and potential new events.103The federal government should also host specific conversations on how to establish mechanisms to coordinate cyber enforcement actions with the private sector. Agencies should also identify annual association conferences104and private sector cybersecurity events105where senior government leaders can speak to further highlight the administration’s efforts and promote partnerships.
Objective 8: Develop uniform metrics to inform and improve data reporting, victim response, and national data collection for federal and SLTT law enforcement.
8.1 The ONCA should consult with relevant federal departments and agencies to develop uniform metrics to evaluate the federal government’s efforts to reduce cybercrime and to inform data collection efforts (101-180 Days).
The 2018 National Cyber Strategy listed objectives to reduce cybercrime, but no metrics to assess the federal government’s efforts.106A 2020 GAO report found that due to the lack of metrics within the 2018 National Cyber Strategy, “[federal] entities may not understand what they should try to achieve or the steps required to produce the desired results.”107Some departments and agencies—like DOJ and USSS—have created metrics related to prosecutions and the prevention of financial losses, but they may not provide a full picture of how effective the US government is at preventing and mitigating the consequences of cybercrime.108For instance, DOJ assesses its ability to recover private sector financial losses based on the FBI’s Internet Crime Complaint Center (IC3) data, but given that IC3 accounts for only 10-12% of all reported cybercrime, achieving that metric may be inadequate.109Further, where these metrics do exist, they are spread out across various agency reports and do not reference each other, further impeding policymakers’ ability to make informed conclusions on the US government’s ability to reduce cybercrime.
The ONCA should consult with relevant departments and agencies to develop uniform metrics across the federal government. Specifically, the ONCA should:
- Consult with OMB to include in the cybersecurity crosscut (Recommendation 7.1) the metrics that departments and agencies with cyber enforcement missions will use to evaluate the impact of their efforts in reducing cybercrime and imposing consequences on perpetrators.110
- Include in the FY 2023 and/or FY 2024 Budget Request funds for the National Institute of Standards and Technology (NIST), or a grant for the National Science Foundation (NSF) or a federally funded research and development center (FFRDC), to conduct a study on the current mechanisms that the US government uses to measure and evaluate its effectiveness in combating other types of crime and determine whether they would be applicable to cybercrime.111
- Examine the benefits of moving to a harm-based approach to cybercrime and determine what other impacts, other than financial loss, should be considered when assessing the effect of cybercrime on specific victims (e.g., vulnerable populations).112
- Supplement traditional law enforcement metrics (indictments, arrests, convictions) with disruption-focused metrics (number of victim individuals/companies for whom risk is mitigated, number of networks defended, etc.) to assess if the expansion of disruption actions are warranted in defined cases, where more focused and unified disruption efforts could result in significant cost savings and protection of victims (see Recommendation 6.1).
8.2 The DOJ and FBI should develop policies and legislative proposals to expand cybercrime categories in the National Incident-Based Reporting System (NIBRS), further spur the uptake of NIBRS, and explore other initiatives to improve data reporting (1 Year+).
Traditionally, SLTT law enforcement agencies report crimes to the federal government through the Uniform Crime Reporting (UCR) Program, which collects data through the Summary Reporting System. The UCR is in the process of transitioning into a broader data collection system called NIBRS by January 2021.113Two prominent challenges, however, exist with NIBRS. First, of the 50+ offenses listed in NIBRS, only one—“hacking/computer invasion”—is designated for cybercrime, potentially leading to a vast undercount of its occurrence.114Second, only half of SLTT law enforcement agencies submitted data to NIBRS in 2019.115As a result, federal and SLTT leaders lack data to make informed policymaking decisions.
The DOJ and FBI should develop policies and recommend legislative proposals to overcome challenges associated with NIBRS by:
- Consulting with the Criminal Justice Information Services Advisory Policy Board (CJIS APB)116to review the National Academy of Science’s 2016 and 2018 Modernizing Crime Statistics Reports’ proposals on including cybercrime categories in NIBRS.117The FBI and CJIS APB should consider whether the proposal to use a yes/no flag to indicate if a crime was cyber-related and whether “the use of computer data or computer systems was an integral part of the modus operandi of the offense”118would sufficiently cover the most common cybercrimes identified by DOJ’s 2018 Cyber Digital Task Force Report.119CJIS APB should also consider whether additional categories need to be included based on Recommendation 8.1.
- Clarifying and emphasizing that federal grants—like DOJ’s Byrne Memorial Justice Assistance Grant (JAG) program and the State Justice Statistics Program for Statistical Analysis Centers120—can be used for cybercrime reporting efforts. Contingent upon assessments recommended in Objective 11, DOJ should also request more funding for those grant programs in their FY 2023 and/or FY 2024 and subsequent budget requests and, if granted, earmark a percentage of each grant to cybercrime data collection efforts.121
- Working with Congress to pass legislation, similar to the Hate Crime Statistics Act122and the William Wilberforce Trafficking Victims Protection Reauthorization Act,123to mandate the collection of cybercrime data through NIBRS. Any legislation should also ensure that federal agencies are required to report relevant data as well.124
- Requiring all federal law enforcement agencies and programs with cyber enforcement missions—including programs like IC3 and iGuardian—to report arrest, incident data, and clearance rates for cybercrime through NIBRS.125
- Returning the IC3 to the more detailed reporting it provided up through 2009, including details on perpetrators of cybercrime in cases where federal law enforcement has been able to investigate and identify them. This should also include requiring IC3 to report on the number of incidents that were investigated and those that led to an arrest or some form of enforcement action. This data should align with the NIBRS reporting framework.126
- Releasing the annual NIBRS report in conjunction with the FBI’s annual IC3 report to provide a comprehensive overview of cybercrime until the IC3 data is accurately represented within NIBRS.127
8.3 To improve law enforcement’s response to victims, the Cybercrime Working Group should develop proposals that improve cybercrime reporting among public and private victims and the assistance awarded to them. (1 Year+).
When asked what crimes Americans worry about, 72% of respondents reported concerns that hackers would steal their personal, credit card, or financial information, ranking it highest among a list of thirteen crimes.128They have reason; public polling reveals that roughly one in four Americans report that they or someone in their household has been a victim of cybercrime. Yet just 1 in 10 reports the crime to law enforcement,129and when they do, the laws and policies on victim restitution for cybercrime victims are unclear and limited.130Private companies, too, report infrequently due to concerns regarding bad publicity and the perception of working closely with law enforcement, which could lead to a loss in profits.131Still, federal and SLTT law enforcement efforts to report statistics and assess their efforts against cybercrime are only as good as the information they receive from victims.
When asked what crimes Americans worry about, 72% of respondents reported concerns that hackers would steal their personal, credit card, or financial information, ranking it highest among a list of thirteen crimes.
To improve data reporting of cybercrime incidents and bolster victim assistance, the Cybercrime Working Group should create policies and legislative proposals to:
- Update the 2012 Attorney General’s Guidelines for Victim and Witness Assistance to explicitly account for victims of cybercrime outside of stolen personally identifiable information.132
- If needed, work with Congress to amend the Victims’ Rights and Restitution Act and the Crime Victims’ Rights Act —which accord certain rights to individuals who meet the statutory definition of “victim” and “harm”—to account for cybercrime.133
- Collaborate with DOJ’s Office for Victims of Crime (OVC) to publish an updated rule that expands the eligibility of the Victim Assistance Program to include victims of cybercrime. The new rule should also detail allowable costs that include legal support services, mental health counseling, and other services as determined by OVC.134
- Assess ongoing efforts to establish a national call center, operated by the Cybercrime Support Network, for members of the public and small and medium-size businesses to report cybercrime and determine how a center would interact with other federal reporting mechanisms.135
- Review the FBI’s implementation of the DOJ Inspector General’s recommendations for improving the FBI’s cybercrime victim notification process.136
- Identify potential victim-reporting challenges with the IC3 and the Federal Trade Commission’s (FTC) Consumer Sentinel Network, including how the agencies interact with those who report a crime and how to deconflict their missions.
- Task DOJ’s Bureau of Justice Statistics (BJS) to conduct a new National Computer Security Survey, which BJS last conducted in 2005, to identify the prevalence of cybercrime among individuals and the private sector.137DOJ should include funds in its FY 2023 and/or FY 2024 budget proposal to conduct this survey, which should be conducted every two years and allow for the anonymization of responses.138
- Provide revisions to DOJ’s “Best Practices for Victim Response and Reporting of Cyber Incidents,” which was last updated in 2015, to provide further information on how the federal government can assist victims of cybercrime.139
- Identify states that limit victim compensation only to victims of violent crime and encourage them to expand it to victims of cybercrime.140
- Create a public messaging campaign for victims on how to report cybercrime, where to report, and describe what happens once law enforcement receives the complaint to illustrate that law enforcement is taking action.
Objective 9: Strengthen federal and SLTT law enforcement’s ability to share investigative information related to cybercrime.
9.1 The Cybercrime Working Group should develop policies and propose additional funding to strengthen existing information sharing mechanisms to enable investigations by criminal justice agencies (1 Year+).
Criminal justice agencies already share investigative information on traditional crime and cybercrime across federal and SLTT jurisdictional lines. The FBI houses the National Data Exchange System, eGuardian, the Malware Investigator, the National Crime Information Center, and a number of nonprofits, such as the National Cyber-Forensics and Training Alliance (NCFTA), also work to facilitate criminal justice agencies’ ability to share, search, link, and analyze information in both unclassified and classified settings.141The FTC also hosts the Consumer Sentinel Network, which allows criminal justice agencies to search a database of scams and identify thefts.142SLTT law enforcement share information through local fusion centers and, in some cases, state-operated cybersecurity and communications integration centers.143States also maintain statistical analysis centers that collect, analyze, and share justice and crime statistics, which could be used to identify national and state-by-state cybercrime trends.144
The Cybercrime Working Group should take the following actions to strengthen existing information sharing mechanisms:
- Collaborate with states that have cybersecurity and communications integration centers145to identify best practices for how states can create or use existing institutions, like the Criminal Intelligence Coordinating Council and state fusion centers, to foster information sharing environments for cybersecurity and cybercrime.146
- Examine how existing investigative information sharing programs can become interoperable to foster users’ ability to search and share information across various platforms.
- Identify and expand additional training on how to use these programs.
- Determine if stronger privacy requirements are needed for current and proposed investigative information sharing programs.
To encourage states to analyze and share cybercrime information, DOJ should also direct BJS to include cybercrime as a “topical area” in its annual State Justice Statistics Program for Statistical Analysis Centers grant program, where it has not been a topical area since at least 2009.147
Objective 10: Improve the digital evidence forensic capacity and capability of federal and SLTT criminal justice agencies by reforming recruitment, training, and retention practices.
10.1 The Office of Personnel Management (OPM) and OMB should issue a memorandum that outlines policy proposals and propose funds for FY 2023 and/or FY 2024 to improve recruitment practices for federal law enforcement agencies regarding cyber enforcement personnel (101-180 Days).
Roughly 32,000 cybersecurity jobs are open in the public sector, with nearly 3,000 of them related to analyst and investigative positions, according to Cyberseek, a grantee of the National Institute for Cybersecurity Education (NICE).148This is likely a vast undercount as “reliable, quantitative information about the cybersecurity workforce is lacking,” according to DHS and the Commerce Department.149This undercount presumably pervades federal law enforcement agencies given that they must compete with the private sector, which can often offer better salaries. Further, women, minorities, and other underrepresented groups have not been adequately recruited from, as highlighted in Part 1 of this report, despite a body of research indicating that diversity leads to better outcomes. Previous administrations took steps to close the cyber-federal workforce gap, but those measures looked at cybersecurity more broadly and did not detail measures for cyber enforcement.150
OPM and OMB should issue a memorandum (similar to their 2016 memorandum)151for executive departments and agencies with law enforcement missions to improve recruitment for cyber enforcement personnel to:
- Include in the President’s Budget Request for FY 2023 and/or FY 2024 additional funding to expand the CyberCorps: Scholarship for Service Program and work with NSF, OPM, and DHS—which operates the program—to prioritize schools that teach competencies relevant to cyber enforcement.152
- Work with DOJ to include in the President’s Budget Request for FY 2023 and/or FY 2024 additional funding to expand the Student Computer and Digital Forensics Educational Opportunities Program, managed by DOJ’s Bureau of Justice Assistance (BJA), to increase the number of students enrolled in digital forensic curricula at higher-education institutions.153
- Establish and/or expand rotational assignments for private sector, SLTT, and federal employees to rotate within federal and SLTT law enforcement agencies to fill short-term positions that may otherwise go unfilled.154
- Mandate that federal law enforcement agencies prioritize implementing the Federal Cybersecurity Workforce Assessment Act of 2015 (FCWAA) so that cyber enforcement positions within the federal government are aligned with the NICE Framework categories.155Fully implementing the FCWAA will help human resource managers identify talent gaps within agencies. Indeed, DOJ found that implementing the FCWAA for the FBI would help “support possible recommendations for introducing new job roles that will improve the FBI’s ability to respond to Internet-enabled crimes and technologically advanced threat actors.”156
- Expand the Pathways Programs—programs that include internships and opportunities for recent graduates—and apprenticeships for federal law enforcement agencies with cyber enforcement mission areas.157
- Improve diversity, equity, and inclusion recruitment methods to reach diverse pools of candidates who are underrepresented in the federal workforce by, for example, recruiting from historically black colleges and universities and engaging in K-12 outreach. The federal government should also continue its efforts to recruit veterans.158
10.2 In their updated memorandum, OPM and OMB should include policy proposals and propose funds to expand training opportunities for federal and SLTT law enforcement and other criminal justice agencies and retain those employees once trained (101-180 Days).
According to CyberSeek, 83% of online job listings for “cybercrime analyst/investigator” require a bachelor’s degree.159Yet at the SLTT level, only 30% of officers have a four-year college degree and only half have a two-year degree.160As a result, a delta exists in the current education levels (at least at the SLTT level) and the competencies needed to perform duties related to cybercrime investigations. However, like other cybersecurity professions, not all law enforcement personnel need a four-year degree to perform cybercrime investigations; some may just need a series of trainings and certifications. Federally funded organizations—such as the NDCAC, NCFI, NW3C, the NCFTA, and others—are therefore paramount to filling this skills gap. Yet, as described in Part 1, some of these organizations, like the NDCAC and NCFI, have been defunded in recent years, limiting how many personnel they can train.161Even with trained personnel, however, public agencies struggle to retain trained employees, who are lured by higher salaries to the private sector.162
OPM and OMB should include in their updated memorandum (see Recommendation 10.1) a requirement that federal departments and agencies with cyber enforcement missions expand training opportunities for personnel and methods to retain them. Specifically, OPM and OMB should:
- Direct DOJ to include funding in BJS’s budget request for FY 2023 to conduct a survey that assesses the competency level of SLTT criminal justice personnel to handle cybercrime cases.163Existing BJS surveys that include cybercrime questions, such as the 2019 National Survey of Prosecutors, could be used as a model.164This assessment could help determine how much federal funding, including grants, should be requested for FY 2024 to sufficiently train personnel. In the meantime, DOJ and DHS should request funding in FY 2023 to replenish the funding that the NDCAC and NCFI have lost in recent years.
- Determine the best agency to create a federal clearinghouse on cybersecurity education, training, and workforce development programs that federal and SLTT agencies can use, with input from SLTT criminal justice agencies.165
- Review how to expand or create a program, in accordance with the NICE Cybersecurity Workforce Framework, within the National Centers of Academic Excellence—a program that provides accreditations to higher education institutions for incorporating cybersecurity curriculums—that is tailored specifically to cyber enforcement needs.166
- Expand the FBI’s cyber certified training and certification program, Forensic Examiner Certification Program, Cyber Executive Certification Program, and USSS Basic Investigation of Computer and Electronic Crimes Program for federal and SLTT criminal justice personnel.167
- Identify federal and SLTT cyber ranges—virtual environments that provide individuals hands-on cyber experience—that could be used to train and certify law enforcement personnel.168OPM and OMB should also determine if programs like the FBI’s Basic School Program, a two-week curriculum designed to instill cybersecurity fundamentals in all employees, can be a model for those ranges.169
- Introduce and/or expand programs to train existing federal law enforcement personnel with limited to no experience working on cybercrime cases, similar to the FBI’s Workforce Training Initiative and On the Job Training Initiative.170
- Work with DOJ so that each US Attorney receives basic cybersecurity and cybercrime training.
- Include digital evidence forensics curricula and other relevant cyber enforcement courses in the Federal Cyber Reskilling Academy, a program dedicated to train current federal employees in non-IT fields to gain cybersecurity skills, to expand training opportunities for non-IT professionals.171
Lastly, once the FCWAA is implemented across federal departments and agencies, agencies should use existing hiring and pay flexibilities for cybersecurity positions by determining if there is “an urgent need” to fill cyber enforcement roles as identified by the NICE Framework.172If retention issues persist after existing authorities are used, federal agencies with these positions should seek legal authority from Congress to create incentive pay for cyber enforcement personnel in exchange for additional service, similar to the incentives pay enumerated under the Uniformed Services Code.173
10.3 The ONCA should work with Congress to develop legislation to ensure that federal and SLTT criminal justice agencies have access to technical assistance to examine digital evidence (0-100 Days).
According to a 2018 Center for Strategic and International Studies survey, only 45% of local law enforcement has access to adequate digital evidence resources.174A 2014 DOJ survey also found that despite 79 publicly-funded crime labs offering dedicated digital evidence support services, large geographical areas exist that require personnel to travel “far distances if they seek the kind of assistance that cannot generally be provided remotely.”175For nearly every crime involving digital evidence, this lack of forensic capabilities creates bottlenecks that can delay investigations.176
To address these challenges, the ONCA should work with Congress to draft legislation with provisions similar to those in the Technology in Criminal Justice Act of 2019.177These provisions should include promoting public-private partnerships to improve law enforcement’s access to digital forensics technology, reviewing federal assistance to SLTT partners, and creating and leveraging grant programs to support training, education, and technical assistance for criminal justice personnel to improve their capacity to analyze digital evidence. Grant programs that enhance SLTT digital forensic capabilities should also require grantees to create policies that retain digital evidence for an appropriate period and preserve suspect, victim, and third party privacy.
Additionally, the ONCA should work with Members of Congress to re-authorize the NCFI, which is set to expire in 2022, and ensure it has the required resources to fulfill its mandate.178
10.4 DOJ should develop policies and request sufficient funding so federal and SLTT criminal justice agencies have access to technical assistance to examine digital evidence (0-100 Days).
While the above legislation is pending, DOJ should also develop similar policies and request funding to advance these goals.
Specifically, DOJ should:
- Recommend, either by developing and/or identifying existing certification programs, voluntary guidelines for personnel who handle digital evidence and for prosecutors, defense attorneys, and judges who use it during court proceedings. These guidelines should also include an overview of cases relevant to digital evidence extraction and handling.179Contingent upon the assessments recommended in this roadmap, DOJ should also request additional funding for relevant grants to train SLTT criminal justice personnel towards the certification.180
- Request funding in the FBI’s budget request for FY 2023 or FY2024 to create and/or expand Regional Computer Forensic Labs—17 federal labs that the FBI manages that convenes federal and SLTT law enforcement agencies to conduct digital forensics activities and assist in investigations—to ensure SLTT law enforcement officials have timely access to their services.181
- Direct the BJA to encourage grantees to the Paul Coverdell Forensic Science Improvement Grants Program to use their funds to support and/or create digital forensics labs. Contingent upon the assessments recommended in this Roadmap, DOJ should also request additional funding for this grant program in FY 2023 and/or FY 2024 to support additional funds for these purposes.182
Objective 11: Assess the needs, resources, and capacity of SLTT criminal justice agencies and federal-state collaborative organizations to address cybercrime.
11.1 DOJ should coordinate with DHS to assess the gap between the needs of SLTT criminal justice agencies and their capabilities and capacities. (0-100 Days).
In 2013, the Police Executive Research Forum conducted a survey of SLTT law enforcement on their cybercrime capabilities183and found significant challenges, including a lack of staffing, funding, and in-house experience. Alarmingly, one county stated that their clearance rate for cyber-related cases was only 10%. These agencies also heavily relied on federal agencies; 66% of SLTT respondents referred cases to the FBI, 51% referred them to the USSS, and 30% to federal task forces.184Yet, these agencies are not at fault due to the challenges and environments that have been previously discussed: a federal reporting system that does not prioritize or calculate the occurrence of cybercrime, a lack of metrics to assess their efforts, victims not reporting crimes, and prioritization of other issues at the SLTT level.
Due to limited survey data, the federal government lacks insight into their SLTT partners' ability to receive, investigate, and prosecute cybercrime at a macro level. As a result, the federal government and Congress does not have the data it needs to inform good policies, laws, and funding decisions.
DOJ and DHS should perform a needs assessment to examine SLTT criminal justice agencies’ ability to:
- Access and analyze digital evidence.
- Provide the required data to NIBRS per Recommendation 8.2.
- Train law enforcement personnel on “basic” cyber enforcement operating procedures, such as how to handle digital evidence and submit digital evidence requests to providers.
- Train attorneys (including public defenders), prosecutors, clerks, and judges on how to use and interpret digital evidence during judicial proceedings.
- Engage with federal agencies on cybercrime cases (see Recommendation 11.3).
To conduct this assessment, Congress could consider providing a grant to a nonprofit organization or require the assessment as a condition of grant funding.185This assessment should also take into account any proposals developed under Recommendations 6.1 and 11.3 that focus on federal and SLTT coordination.
11.2 DOJ should determine how many localities are using the JAG program for cybercrime initiatives, how much these localities have received for these initiatives, how the program could be used to promote SLTT cyber enforcement, and whether other grant programs should be expanded (0-100 Days).
While several federal grant programs exist that SLTTs rely upon for a variety of needs,186DOJ’s BJA primarily provides federal criminal justice funding to SLTT entities through the JAG program. These funds are used to provide additional personnel, equipment, supplies, contractual support, training, technical assistance, and information systems.187BJA also lists “JAG Areas of Emphasis” to “encourage state and local jurisdictions to support projects” based on BJA’s priorities. None of these cover cybercrime.188The amount that states are allotted is based on the state’s population and the number of reported violent crimes in the state (Part 1 Crimes as collected by UCR/NIBRS).189JAG does not preclude SLTT agencies from using funds for cybercrime needs, but notwithstanding Americans’ heightened concern about falling victim to cybercrime, combating cybercrime is deprioritized compared to violent crimes.190
To ensure that JAG emphasizes cyber enforcement, DOJ should direct BJA to:
- Review previous grant awards to determine how many applicants have used JAG grants to improve their cyber enforcement capacities and the total amount of JAG funds used for those purposes.
- Include cyber enforcement initiatives as an “Area of Emphasis” for FY 2021 JAG grants and future JAG grants.
- Encourage grant applicants to add an addendum to their JAG strategic plan to describe how this funding could be used to bolster their cyber enforcement capabilities through FY 2024.191
- Explicitly detail in the Notice of Funding Opportunity that cyber enforcement tools, programs, initiatives, and personnel can be funded by JAG, provided that applicants can show how they would sustain such programs and personnel, either through future JAG funding or SLTT expenditures.192
- Collaborate with the FBI and the CJIS APB to consider including categories of cybercrime as Part 1 crimes to encourage SLTT agencies to report cybercrime through NIBRS and to ensure that funds are allocated to those areas with high rates of cybercrime. Alternatively, BJA, FBI, and the CJIS APB could work with Congress to amend the JAG statute to include rates of cybercrime as part of the formula for allocating JAG funds to states.193
DOJ should also examine other grants, like the Community Oriented Policing Services program, to determine if they can emphasize and/or include cyber enforcement funding opportunities.194And as mentioned previously, DOJ should look at other BJA and National Institute of Justice grants, like the Student Computer and Digital Forensics Educational Opportunities Program, State Justice Statistics Program for Statistical Analysis Centers, and the Paul Coverdell Forensic Science Improvement Grants Program, to develop SLTT capabilities and capacity.
11.3 DOJ and DHS should identify and recommend proposals on how to improve federal and SLTT investigative and prosecutorial coordination (0-100 Days).
Because cybercrime crosses various geographical and legal jurisdictions, the federal government has created and expanded several cybercrime task forces throughout the states to foster collaboration. However, monetary thresholds prescribe when federal agencies get involved, and as a result cases that don’t meet that threshold are often left unresolved due to limited capacity at the local level.195Further, the DOJ Inspector General found that attracting participants to engage in task forces, like the FBI’s Cyber Task Force, is difficult because SLTT law enforcement agencies “believe that cyber intrusion investigations are inherently a federal matter, or [lack] the resources or personnel to detail an officer to the local Cyber Task Force.”196
To foster federal and SLTT law enforcement coordination and partnership, DOJ and DHS should examine the FBI’s Cyber Task Forces,197the Internet Crimes Against Children Task Force Program,198the FBI’s Violent Criminal Apprehension Program,199Joint Terrorism Task Forces,200the USSS Cyber Fraud Task Force,201and other task force models to assess what current collaboration vehicles can be enhanced to strengthen federal and SLTT coordination. This examination should also include incentives for SLTT law enforcement agencies to participate in task forces, as lack of resource incentives has been a repeated obstacle for participation.202
Global Cybercrime Cooperation
Objective 12: Establish a new DOS structure to ensure a well-resourced single point of high-level leadership for all cyber diplomacy matters, backed by an architecture that allows for other bureaus advancing policy and programming on cybercrime to effectively coordinate.
12.1 The Secretary of State should establish an Office of International Cyberspace Policy at DOS with the head of Office having the rank and status of Ambassador and ensure this Office is supported with the adequate funding and personnel to fulfill its mandate (0-100 Days).
The Office of the Coordinator for Cyber Issues was established in February 2011 to spearhead DOS’s global diplomatic engagement on cyber issues and coordinate the work of DOS’s many regional and functional bureaus that are engaged in these areas.203The United States was the first country to establish such a senior-level official, who was given the title of coordinator. The Office has since been downgraded and placed within the Bureau of Economic and Business Affairs, eliminating its direct connection to the Secretary and sending a signal to America’s allies, partners, and adversaries alike that cyber diplomacy is not a top priority for the US government.
Given the proliferation of cyber threats facing the United States and the lack of top-level US diplomatic leadership on these issues, the Secretary of State should establish an Office of International Cyberspace Policy at DOS led by an experienced official appointed by the President with the rank and status of Ambassador to restore America’s leadership globally on cyber diplomacy. The Office should be established in such a way to ensure it:
Has direct access to the Secretary. The Secretary should consider whether the Office for International Cyberspace Policy should be made a full DOS bureau and whether the head of such an Office should be appointed at the rank of Assistant Secretary or higher.204While this position may report to an Under Secretary, it could also be given the authority to report directly to the Secretary without the approval or concurrence of any other official at DOS, as threats and circumstances require.205Should the position report to an Under Secretary, consideration should be given to the chain of command that best ensures it has cross-cutting authority as referenced below.
Has cross-cutting authority to coordinate DOS’s efforts on the full spectrum of international cyberspace policy issues, including cybercrime. The Office should have duties such as those outlined in the bipartisan Cyber Diplomacy Act of 2019 to oversee all aspects of international diplomacy related to cybercrime, cybersecurity, deterrence, Internet access, Internet freedom, the digital economy, the development of international norms of responsible state behavior in cyberspace, and other emerging challenges facing the United States in cyberspace.206This should also include ensuring the head of Office is able to:
- Serve as the principal cyberspace policy official, including on cybercrime, within the senior management of DOS and as the advisor to the Secretary of State for cyberspace issues;
- Serve as the principal advisor on cyber threat prioritization within DOS and ensure that the various bureaus and offices adopt plans in line with this prioritization and dedicate the needed attention and resources they deserve;
- Lead DOS’s diplomatic cyberspace efforts, including on cybercrime, in coordination with other DOS bureaus and offices, as well as other executive departments and agencies of the US government, or support other federal entities when more appropriate for them to lead such diplomatic engagement;
- Advocate for the inclusion of cyber priorities in rule of law programming administered or supported by all DOS regional and functional bureaus and promote this in engagement with corresponding assistant secretaries;
- Promote the building of foreign capacity on cyber, in coordination with other DOS bureaus and executive entities, and support the establishment of clear metrics to monitor and evaluate the effectiveness of such capacity building;
- Promote and protect the exercise of all human rights and respect for the rule of law and civil liberties, including by supporting and consulting civil society groups working to advance such efforts, and considering strategies for mitigation on the misuse of capacity building, technical assistance, technology, and other areas of support provided by DOS to foreign governments; and
- Promote diversity, equity, and inclusion within the Office of International Cyberspace Policy staff—including through increasing the participation of more women, minorities, and other underrepresented groups—and encourage such representation in international cyber forums and programs, policies, and initiatives administered by DOS to build foreign cyber capacity.207
Has sufficient personnel to fulfill its mandate. The Secretary should ensure the Office is headed by an individual with experience on cyber issues and diplomacy and is sufficiently staffed to fulfill its mandate and the objectives of an updated International Cyber Engagement Strategy (see Recommendation 13.1 below). The Secretary should task all heads of Department bureaus and offices with appointing a senior-level person to serve as their representative to the Office of International Cyberspace Policy and attend meetings as requested.208
Has the authority to offer input into how cyber funding is spent by the Department. The Office, in coordination with the Office of Foreign Assistance and Office of Budget and Planning, should task all bureaus and offices along with all entities at the US Agency for International Development (USAID) with assessing how much of their previous fiscal year budget was spent on any cyber-related programming, personnel, or policy efforts.209With this baseline, budgetary tracking systems should be updated so the Office of International Cyberspace Policy can receive annual updates and establish a process to provide input into how general funds, such as Economic Support Funds, are disbursed to functional and regional bureaus to ensure cyber issues are prioritized. The Office should also work with relevant department stakeholders to develop a universally accepted definition of "cyber," accounting for the federal government definition of cybercrime in recommendation 6.1, to assist and enable bureaus and offices to track cyber spending.
Has the authority to set overall key indicators and performance goals related to cyber and to coordinate with other functional and regional bureaus on their cyber-related indicators and performance goals. DOS’s annual performance report includes cyber-related performance goals and indicators.210Not only should the Office have the authority to set such indicators and performance goals, but functional and regional bureaus should be required to consult with the Office before setting any cyber-related indicators and performance goals.
Serves as the co-chair of all international cyber interagency policy committee (IPC) meetings, if appropriate in the broader IPC process. IPC and sub-IPC meetings serve as an important forum for key officials and experts inside of the US government across departments and agencies to discuss cybercrime and other cyber-related threats that require international cooperation to address. To the extent it is appropriate in the broader IPC process, the Office should serve as the principal co-convener of such IPCs along with the proposed ONCA (see Objective 1) at the White House.
12.2 The White House should work with Congress to codify the Office of International Cyberspace Policy at DOS (0-100 Days).
Disagreements between DOS and Congress have prevented legislation from moving forward that would codify this Office. We believe the approach of the Cyber Diplomacy Act should be a baseline for future legislation. This legislation should ensure the Office is not placed in a chain of command at DOS that may inhibit work on the wide range of issues required to make progress on cyber enforcement while safeguarding human rights and promoting the rule of law.
Objective 13: Identify a set of diplomatic tools and policy options to boost international cooperation in cybercrime investigations and address governments that are systematically uncooperative.
13.1 DOS, in coordination with the White House and all relevant departments and agencies in the US government, including the IC, should draft a new US global cyber engagement strategy through an interagency process. This strategy should be updated every four years and inform the development of a national cyber strategy by the White House (1 Year+).
DOS previously led an interagency process to draft an Engagement Strategy for International Cooperation in Cybersecurity, which was incorporated into the 2018 National Cyber Strategy.211DOS should lead an interagency process to draft a new global cyber engagement strategy that includes both public and classified portions and a corresponding implementation plan. This process should align with the ONCA’s update of the National Cyber Strategy (see Recommendation 5.3). The NIE called for in Recommendation 4.5 should be conducted before the global cyber engagement strategy and transmitted to DOS to inform the development of this strategy.
This new global cyber engagement strategy should cover the full spectrum of cyber-related priorities for the United States, recognizing that cybercrime has not received the attention it deserves in previous DOS strategies and must be a central focus of this and any other cyber-related strategies moving forward. This strategy should include:
- An assessment of the goals, objectives, and indicators that will be used to guide the US government’s efforts to promote a free, open, and secure Internet, expand the US government’s allies and partners on cyber-related issues, and induce behavior change in states playing a role in cybercrime and/or other forms of malicious cyber activity.
- An evaluation of the effectiveness of current and previous US bilateral and multilateral diplomatic engagements in expanding US partners and allies on cyber-related issues, and a strategy for strengthening such efforts, including a determination of how the US government can be more active in pushing international organizations to expand their cybercrime engagement.212
- A strategy for DOS and DOJ to work together to increase the number of Member States that accede to the Convention on Cybercrime of the Council of Europe (Budapest Convention).213This should include an assessment of the effectiveness of US government messaging on the benefits and opportunities afforded to States that join the Budapest Convention and of US capacity building efforts and technical assistance to facilitate membership in this Convention.
- An evaluation of whether DOS’s current level of resources, both in budget and personnel, is adequate to achieve the stated goals and objectives. DOS should also assess whether it currently has the level of expertise in key bureaus and missions, particularly missions to the UN and other international organizations, needed to advance US priorities on cybercrime, cybersecurity, and other cyber issues.
- A classified annex with an individualized plan for each country the IC determines is abetting, ordering, or conducting cybercrime and/or other forms of malicious cyber activity, including objectives for deterring and responding to such activity, tools to deploy to do so, and clear roles and responsibilities assigned to entities in US government departments and agencies.
- A classified list of principles, which could include general talking points, to guide heads of state or minister-level engagement by the President or Secretary of State, Attorney General, or other cabinet-level officials with foreign counterparts to raise cybercrime and other cyber-related diplomatic priorities, including accession to the Budapest Convention.
- An implementation plan and timeline that includes an assigned lead implementing entity in the US government and budgetary estimates where applicable.
- A delineation of the roles and responsibilities on global cyber engagement, including cybercrime, throughout the US government as determined by the ONCA (see Recommendation 6.1). This should include a plan for strengthening cooperation, coordination, and transparency on these issues between DOS and USAID.
- A plan for formalizing the DOS’s engagement with the private sector and civil society groups on global cyber issues. This may involve soliciting their views on bilateral and multilateral negotiations, when appropriate, and discussing partnerships to promote responsible state behavior in cyberspace and advocating for behavioral change in states that are systematically unwilling to cooperate in cybercrime investigations. This engagement should also explore how US-funded foreign cyber capacity building programming can better align with new technological developments and best practices in cybersecurity.214In establishing this plan, DOS must recognize that the “private sector” and “civil society” are not monoliths and ensure diversity in representation and perspectives.
- A plan to strengthen US leadership in forums aimed at establishing cyber norms, rules, and principles to guide state behavior in cyberspace. This should include the promotion and enforcement of norms previously agreed upon, consideration of US membership in the Paris Call for Trust and Security in Cyberspace,215and promotion of the norms established by the Global Commission on the Stability of Cyberspace.216The US government should continue to reaffirm international law is applicable to cyberspace and impose consequences on states that violate international norms, particularly those that disrupt or attack critical infrastructure. Norms on cybercrime cooperation have largely remained voluntary and non-binding for many reasons, including that cybercrime has historically been viewed as a tool of non-state actors. With the increasingly blurred line between state and non-state actors on cybercrime, such a plan should detail how the US government might work to strengthen such norms on cybercrime cooperation and explore links between norms of state behavior and cyber stability and those on cybercrime. It should also assess how partnerships with the private sector and civil society can be better leveraged to enforce these norms.217
- A recognition that the US government must engage with foreign governments on cyber-related issues in a reciprocal fashion. The United States has often made demands of foreign governments that it is not able or willing to uphold itself, such as in the timely response to cross-border data requests or the implementation of cyber norms, rules, and principles guiding state behavior in cyberspace. If the US government wants to advance cooperation with foreign governments on a wide range of cyber issues, then it must be willing to assess areas where its own actions might hinder progress.
13.2 Once a new global cyber engagement strategy is issued, all regional DOS bureaus and USAID should update or draft regional cyber strategies to align with the newly established goals and objectives (1 Year+).
DOS has previously created regional cyber strategies to implement its global cyber strategy.218These bureaus should be required to draft new or update previous regional cyber strategies to align with a new DOS-wide cyber engagement strategy, and do so following all subsequent strategy updates every four years.
13.3 DOS should include cybercrime and other cyber priorities in other key review and strategic planning documents for the Department and USAID. This should include any and all future Quadrennial Diplomacy and Development Reviews (QDDR) (1 Year+).
In addition to issuing a new global cyber engagement strategy and setting specific cyber performance goals and indicators, DOS should include a specific component on cybercrime and other cyber issues in all DOS strategic review and planning documents. If DOS conducts another QDDR,219it must ensure that cybercrime, cybersecurity, and other cyber issues be a key standalone priority. While the 2010 QDDR laid out the case for an Office of the Coordinator for Cyber Issues and highlighted the need to work through NATO and with NATO allies to boost cyber capabilities,220the 2015 QDDR only made passing reference to this priority. The world has changed dramatically since this last QDDR, with increasingly blurred lines between state and non-state malicious cyber activity, growing digital authoritarianism, and a fragmenting of cyber norms. Any future QDDR or other strategic planning and review processes must reflect these developments and describe how DOS will meet the objectives established in the global cyber enforcement strategy, including through bureaucratic and institutional reforms and dedicated resource streams.
13.4 DOS should enhance its training and awareness raising on cybercrime for policy officers at posts, encourage posts to add cybercrime as a standing item to Law Enforcement Working Groups, identify additional Department-wide training opportunities to enhance training and awareness on cybercrime, and dedicate time at annual Chiefs of Mission meetings for updates on cyber developments (101-180 Days).
DOS should improve its training on cybercrime-related issues for policy officers sent to posts and highlight the role of and support that can be provided by DOJ, FBI, and other US government personnel at posts in cybercrime cases. DOS should also encourage posts to add cybercrime as a standing item for their Law Enforcement Working Group. The Office of International Cyberspace Policy should also identify additional DOS-wide opportunities to train and raise awareness of cybercrime issues among personnel, including those in the Foreign Service. Further, the head of the Office of International Cyberspace Policy should be invited to present on global cyber developments, including trends in cybercrime, before the annual Chiefs of Mission meeting whenever possible and relevant.
13.5 The Department of Treasury, in coordination with all other relevant departments and agencies including the IC, should undertake an inter-agency assessment of the effectiveness of all existing cyber-related sanctions in halting or reducing malicious cyber activity (101-180 Days).221
It has been over five years since President Obama issued the first executive order to establish a dedicated cyber sanctions regime in the United States. Since then, the Treasury Department has largely imposed sanctions under this regime on individuals and entities in four countries: Iran, Russia, North Korea, and China.222A review of these sanctions indicates an overwhelming majority are suspected of having links to nation-state entities.223With the European Union (EU) following suit last year, the United Kingdom moving forward with its own cyber sanctions regime, and the Treasury Department’s June 2020 announcement that it has sanctioned six Nigerian nationals for a cybercrime scheme,224the time is ripe for an inter-agency, holistic assessment of the impact of US cyber-related sanctions. The Treasury Department should institutionalize this review every four years, in conjunction with the update of DOS’s global cyber engagement strategy (see Recommendation 13.1) and the White House’s National Cyber Strategy (see Recommendation 5.3).
Such an assessment should include:
- A determination of the effectiveness of sanctions in changing or deterring behavior of the intended target(s). And if such behavior has neither changed nor been deterred, an IC evaluation as to why not. This determination should take into account any relevant research from outside the US government.
- An evaluation as to whether the issuance of further cyber-related sanctions could weaken or strengthen existing sanctions, including consideration of IC assessments on the expected reciprocal actions from the targeted actors or governments.
- Based on the above evaluation, a determination as to whether the decision-making framework for the issuance of cyber-related sanctions should be updated.
- An analysis of the application of sanctions to target non-state cybercriminals and the expected outcome of such a tool on non-state actors.
- A strategy for US diplomatic efforts to advocate for additional cyber sanctions regimes in non-EU countries, including considering whether the US government should advocate for a multilateral cyber sanction regime.
- An assessment of the effectiveness of the US government’s public or private messaging on individual(s) or organization(s) currently sanctioned for malicious cyber activity, including the specific behavior that such sanctions are targeting and how changes in their behavior will lead to a lifting of sanctions.
13.6 DOS, in cooperation with the Department of Treasury, should increase support to non-governmental research institutions to conduct regular, independent assessments of the effectiveness of cyber sanctions and propose recommendations to improve the US’s cyber sanctions regime (1 Year+).
GAO found in 2019 that US government agencies have not determined whether sanctions actually “work” and are not required to do so.225As cyber sanctions have increasingly become a tool in America’s cyber diplomacy toolbox, agencies should invest resources to study whether these sanctions are working. Fortunately, there are numerous FFRDCs, non-profit think tanks, and academic institutions with the necessary expertise on US sanctions policy. Instead of solely relying on the US government’s own internal assessment of its cyber sanctions efforts, DOS, in partnership or cooperation with Treasury, should support institutions doing regular, independent expert evaluations on the effectiveness of US cyber sanctions.226
GAO found in 2019 that US government agencies have not determined whether sanctions actually “work” and are not required to do so.
13.7 Should the United States choose to participate in negotiations on a new global cybercrime convention, it should develop a strategy for engagement and ensure the process is transparent, inclusive, and safeguards human rights (1 Year+).
Negotiations on a new global cybercrime treaty, sponsored by Russia, may begin in earnest in 2021. The US government unsuccessfully opposed a UN General Assembly resolution in 2019, which was sponsored by Russia and had the support of China and a number of other Member States, to begin negotiations on a treaty.227Such a treaty threatens to undermine progress that has been made on the Budapest Convention. Human rights and other civil society organizations have expressed deep concerns about the framing of the Russian resolution and draft treaty provisions Russia previously circulated.228
A determination by DOS as to whether the United States will participate in substantive negotiations should be made after the process and procedures are established. If the US government chooses to participate, it should develop a strategy for achieving US objectives, including the following actions:
- DOS should be the lead US government agency in these negotiations, supported by DOJ and any other relevant US government entities as necessary. DOS should designate a senior-level official as the lead negotiator and ensure that the UN’s secretariat and the chair of any negotiations have a direct line to this individual and/or their staff.
- The US government, led by DOS in partnership with DOJ, should work with allies and partners to push for a formal consultative mechanism to ensure private sector and civil society organizations can share their recommendations, perspectives, and concerns throughout the negotiation process and are well briefed on developments in the negotiations. Without input and partnership from the private sector and civil society, any binding mechanism for global cybercrime cooperation will be wholly ineffective.
- The US government should advocate for strong human rights and rule of law safeguards that, at a minimum, meet the safeguards required for membership in the Budapest Convention and look to go even further. The US government position should reflect its regular consultation with groups focused on digital and human rights (including those focused on gender, civil liberties, and digital and racial equality) and other particularly affected constituencies.
- The US government should be prepared to walk away from such negotiations if it becomes clear that strong safeguards to protect human rights, democracy, and the rule of law will not be considered.
Objective 14: Identify a group of countries where the US government is not receiving timely assistance in cybercrime investigations and develop programs to support their criminal justice capacity building needs—including operational support, policy development, and harmonization of laws—to boost cooperation.
14.1 As part of the development of a new global cyber engagement strategy, DOS should work in cooperation with USAID, DOJ, FBI, the IC, and all other relevant federal entities to develop an assessment, monitoring, and evaluation (AM&E) framework for all cyber foreign capacity building programs funded through annual foreign assistance resources. This AM&E framework should inform and ultimately be integrated into a broader DOS security-sector assistance AM&E framework (181 Days – 1 Year).229
Despite progress, DOS still lacks a comprehensive, holistic AM&E framework that is universally used across DOS for security assistance programming. This hinders DOS’s ability to determine the efficacy and impact of all foreign assistance programming aimed at building partner governments’ security capacity. Developing a universal framework will take time and resources, but DOS can immediately begin developing an AM&E framework specifically for cyber foreign capacity building programs that includes cybercrime as a critical area of focus and that aligns with any work underway to develop a universal framework.230A cyber AM&E framework would enable more informed decisions on the allocation of resources, inform the prioritization of certain countries and capacity building areas, and allow for a regular, systematic evaluation of cyber capacity building programming. Establishing a cyber AM&E framework will take a significant amount of time and resources, but without it DOS will be unable to assess the impact of its cyber capacity building even as cyber threats become a predominant national and economic security threat for many countries. As such, DOS must dedicate adequate personnel and funding to establish this framework and ensure such resources are reflected in the annual budget submitted to Congress if necessary.
DOS should ensure that an AM&E framework for cyber is aligned with what should be a Department-wide AM&E framework for all security assistance programs. Otherwise, DOS will be less able to measure progress and impact of cyber capacity building in relation to other security assistance programs, leading to a piecemeal approach to capacity building in recipient countries.
The US government has invested foreign assistance resources into programs aimed at enhancing the capacity and capability of foreign criminal justice entities—particularly investigators, computer forensic experts, and prosecutors—to investigate and prosecute cybercrime and develop regional and global networks to assist in these efforts. However, a more comprehensive framework than what currently exists is needed to determine the size, scope, and impact of such programming and all cyber capacity building programming resourced through foreign assistance accounts.
The establishment of a cyber capacity building AM&E framework should:
- Include a baseline assessment and allow for further regular assessment of all cyber capacity building programs and their corresponding budget levels (whether funded by State or Foreign Operations resources).231
- Establish a minimum monetary threshold for capacity building projects that will be required to be assessed and use the established AM&E framework for cyber capacity building programming. Such a minimum monetary threshold should ensure at least half of cyber capacity building programs and projects supported by foreign assistance funding would be required to use this framework.
- Document all federal bureaus and offices that support and/or implement significant cyber capacity building initiatives, including those focused on bolstering the capacity of global criminal justice actors to fight cybercrime and other malicious cyber threats.
- Set short, intermediate, and long-term objectives for each program or project and regularly assess whether objectives are being met. Such objectives could include building or strengthening support for the US government’s broader goals to promote a free, open, and secure Internet.
- Evaluate, as informed by any relevant IC analysis, the likelihood that objectives will be met and the potential impact on security sector politics and human rights. This will ensure that cyber capacity building programs do not have unintended impacts on broader US government objectives and that an AM&E framework can be used to regularly monitor potential abuse or misuse of such programs (as has been observed in a number of countries).232Such an assessment should inform metrics that will allow program managers to monitor and evaluate whether unintended consequences are occurring and set guardrails to discontinue support if needed.
- Require all assessments, starting with the program design phase, to integrate a gender analysis to assess the potential impacts of security assistance programming on women and men, girls and boys, in line with the commitments in the Women, Peace, and Security Act of 2017233and analyze the differential impacts of such programming on other social identities.
- Align with all existing DOS monitoring and evaluation framework processes234and establish a baseline and indicators to track and measure progress and impact toward set targets while accounting for human rights safeguards and gender considerations. This should allow for a regular examination of the effectiveness and impact of such activities and programs based on these indicators in meeting the established short, intermediate, and long-term objectives. Monitoring and evaluation of programs and projects should consider whether any unintended consequences have resulted from capacity building and, if so, allow for funding to be halted or paused.
- Allow for annual evaluation of programs and for results to be transmitted to DOS’s Office of International Cyberspace Policy, which should use this data, in coordination with other DOS offices, to inform decision-making on the distribution of cyber-related foreign assistance funds.
14.2 The Office of International Cyberspace Policy, in partnership with the International Narcotics and Law Enforcement Bureau (INL) and relevant federal entities, should lead a process that identifies a target number of countries where the US government is not receiving timely assistance in cybercrime investigations and increased support to their cyber capacity building needs may have an impact (1 Year+).
DOS’s INL Bureau receives funding for cybercrime and intellectual property rights (IPR) global capacity building programs through the annual state and foreign operations appropriations bill. However, DOS has attempted to cut the request for this line-item from $10 million to $5 million for the past three fiscal years.235Fortunately, Congress has not fulfilled this request; however, this existing funding pales in comparison to the capacity building support provided for other security threats, such as terrorism.236The continued global cyber enforcement gap makes clear that more capacity building is needed to strengthen the capabilities of governments to combat this threat.237
As part of the drafting of the global cyber engagement strategy (see Recommendation 13.1) and informed by the IC assessment on cybercrime (see Recommendation 4.5), DOS, DOJ, and other relevant federal entities should identify a group of countries where national laws criminalize cybercrime acts as defined by the Budapest Convention (or at least some initial steps have been taken in the direction of such criminalization), but the country’s government has been unable to stop malicious cyber activity at least in part due to issues around inadequate capability and/or policy or legal constraints. This should include governments that are not members of the Budapest Convention, but that DOS determines may be willing and able to meet the qualifications for membership in the future if they have increased capacity to do so.
- Once this group of countries is identified, DOS and DOJ should determine a set of criteria—including the importance of each country to broader US government foreign policy objectives—to be used to select countries for a pilot program for cyber capacity building, with a substantial focus on strengthening cybercrime enforcement capacity. To ensure the effectiveness of such a pilot program, no more than 10 countries should be selected, with a focus on ensuring as much regional diversity as possible.
- DOS and DOJ should work through an interagency process to identify the top capacity building needs of these governments, including operational support, policy development, and harmonization of laws, and either plan to increase bilateral funding toward these efforts or, when appropriate, provide support through international organizations such as the UN.
- DOS should include in its annual congressional budget justification a funding request for this pilot program, plus the additional staffing necessary to support it, and an explanation for how the countries were selected, including how IC analysis informed the process. A classified annex with more specific analysis can be sent to Congress separately.
- The Office of International Cyberspace Policy; INL; the Bureau of Democracy, Human Rights, and Labor; and other key DOS entities should work in cooperation with Congress to identify any areas in existing law that may require changes to allow the US government to build the cyber capacity of security sectors, while still ensuring repressive governments or their institutions are not given support and tools to perpetrate abuses.
- The established AM&E framework should be used to conduct an assessment for each selected pilot program country and monitor and evaluate capacity building efforts annually to assess the impact and effectiveness of such efforts in meeting the established objectives. Should a majority of the short, intermediate, and long-term objectives be met, DOS should look to institutionalize this pilot program as part of the Cyber and IPR global programming executed by State INL and increase its budget and personnel accordingly.
14.3 DOS should take steps to establish regional and/or in-country donor coordination mechanisms on cyber capacity building to overcome the duplication in funding that has been observed from donor governments (1 Year+).
Research has found that the sheer number of global organizations that are involved in cyber capacity building makes coordination among donors particularly difficult.238This can make it challenging to ensure the US government is funding capacity building programs that do not duplicate other donor-supported programs or, worse, work at cross-purposes to each other.
To help overcome these issues, the US government should establish regional donor coordination mechanisms to share more information about its priorities, programming it supports, and the key actors on the ground with which it liaises. DOS should assess whether existing mechanisms such as the US Transnational and High-Tech Crime Global Law Enforcement Network could work to coordinate donors across different regions.239Additionally, DOS should encourage its overseas missions to establish in-country donor coordination mechanisms for cyber capacity building and send guidance to all missions on best practices for doing so. There are many forms of donor coordination models, such as working groups, that help enhance information sharing and advance agreement on priorities between donors that are worth evaluating for cyber capacity building purposes.240
Objective 15: Streamline the process and improve the timeline for responding to cross-border data requests, in accordance with substantive and procedural protections.
15.1 DOJ, in cooperation with DOS, should strengthen prioritization within the US government for the signing of new executive agreements under the Clarifying Lawful Overseas Use of Data (CLOUD) Act, institute transparency in the process for the negotiation of CLOUD Act agreements, and ensure CLOUD Act agreements are not used as a means for facilitating a backdoor to decryption mandates or other misuses prohibited by the law (Continuous).241
Increasingly, digital evidence is critical to the investigation and prosecution of cybercrime and other forms of crime.242And that digital evidence is often either located across or controlled by entities that cross international borders. This poses challenges for the United States. Given that so much digital evidence is either controlled by US-based companies and/or physically located within the United States, it poses even greater challenges for foreign governments.243US law prohibits US-based companies from disclosing communications content (such as emails or text messages) directly to foreign governments. Instead, foreign governments must make a formal government-to-government request for such data.
The primary means for making these kinds of data requests is through mutual legal assistance treaties (MLATs) or agreements. However, the United States only has treaties in place with less than half of all countries.244And the process, which is managed by DOJ’s Office for International Affairs (OIA), is slow and cumbersome.245In FY 2016, DOJ indicated that each OIA attorney was handling three times a manageable caseload.246While the “MLAT Reform” program, launched in FY 2016, has helped to reduce the backlog at OIA for MLAT requests, the number of pending cases still remained in the thousands as of DOJ’s FY 2019 budget request.247DOJ recently noted that “Such delays prompt calls by foreign governments for data localization, trigger foreign demands that [US] Providers produce information directly in response to foreign orders or face criminal penalties, and encourage foreign proposals that [US] Providers be subject to foreign or global data protection regimes.”248
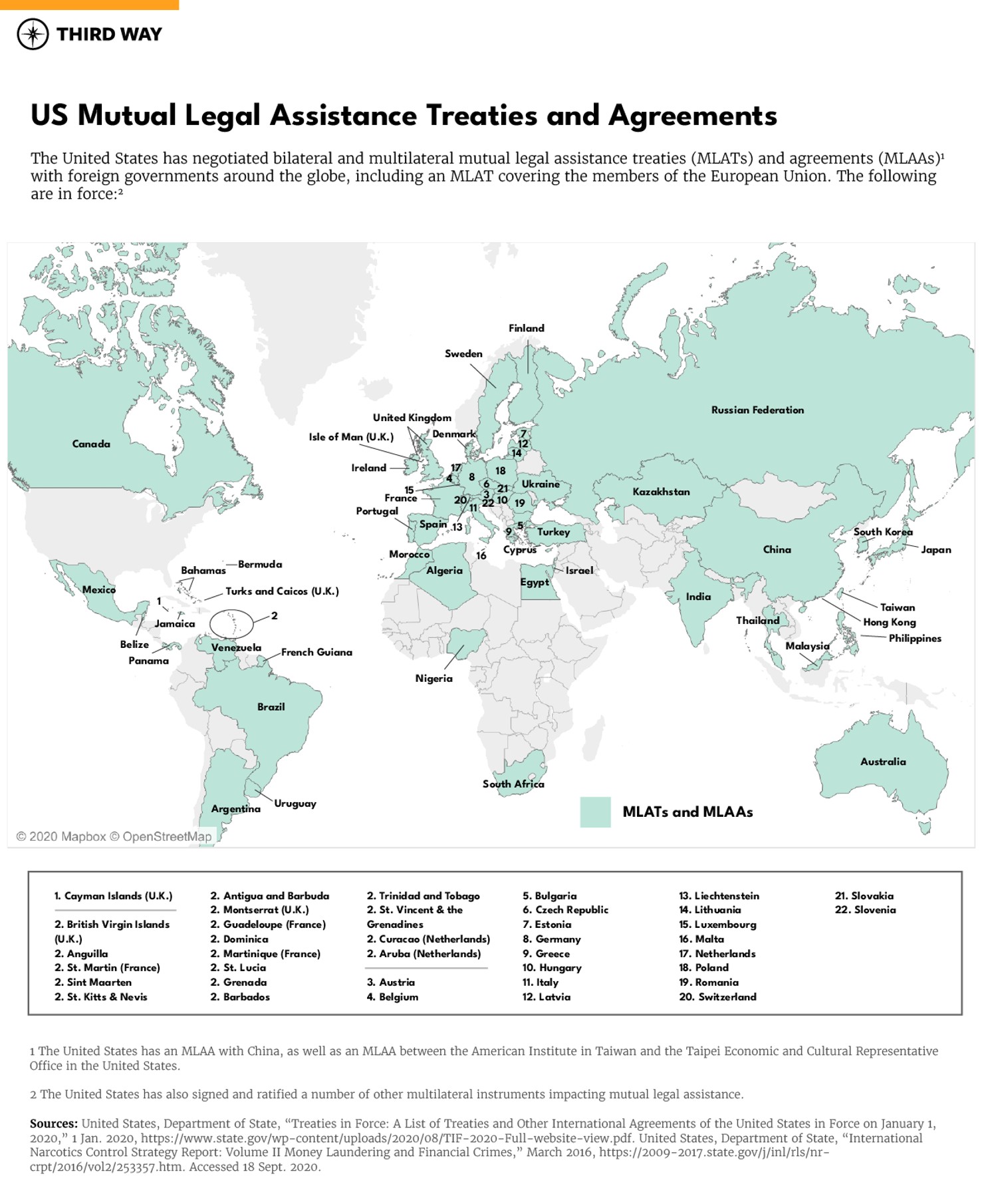
The current backlog for processing requests is not only unsustainable for OIA, it hinders progress in cybercrime investigations globally, which ultimately hurts the United States in bringing to justice the perpetrators of cybercrime. It also reduces the incentive of foreign governments to quickly process requests from the US government for electronic evidence.
The CLOUD Act represents an attempt to alleviate some of this burden, providing a mechanism by which select foreign governments can bypass the mutual legal assistance (MLA) system if they are seeking data about foreigners located outside the United States.249Importantly, only those countries that meet certain human rights and rule of law baselines are eligible to enter into these agreements.250The US government has only entered into such an agreement with the United Kingdom; it is negotiating another with Australia.251
DOJ, in cooperation with DOS, should take several actions to improve the process and procedures for the negotiation of such agreements:
- The Attorney General should make clear the negotiation of CLOUD Act executive agreements is a top priority and ensure that the relevant entities have adequate resources and personnel.
- DOJ should publish CLOUD Act executive agreements, making them accessible to the public. The CLOUD Act requires the Attorney General, in concurrence with the Secretary of State, to certify certain conditions have been made before an executive agreement can be entered into force, and that this certification be published in the Federal Register.252No equivalent requirement exists to make the text of these executive agreements public, but there is also nothing in the CLOUD Act that would prohibit the public release of these agreements.253In fact, the first agreement with the United Kingdom was made public. The Attorney General should make clear that that will be standard practice moving forward to promote transparency in this process, and Congress should make all necessary changes to the statute to ensure this practice becomes law.
- The Attorney General, in cooperation with the Secretary of State, should put in place effective auditing so that the standards and procedures laid out in the Act are met.
- The agreements should explicitly protect against requests being coupled with decryption mandates or other technical assistance orders.
15.2 DOJ should update guidance on the CLOUD Act, as necessary, to clarify for foreign partners and domestic audiences what the law does and does not do and provide information to those that may misunderstand its intent and scope (Continuous).254
In addition to providing updated guidance, DOJ, in cooperation with the DOS, should ensure the network of Resident Legal Advisors, International Computer Hacking and Intellectual Property experts, FBI cyber assistant legal attaches (ALATs), and other personnel deployed overseas to support foreign governments on cybercrime investigations, prosecutions, or capacity building is fully updated on developments with the CLOUD Act and able to provide support and information to foreign partners to understand its purpose and scope, particularly on the powers provided under Part 1 of the law.255
15.3 DOJ, in cooperation with DOS, should work to conclude negotiations around the Second Additional Protocol to the Budapest Convention as a means of facilitating more efficient cross-border data sharing while ensuring due process and the protection of civil liberties, and begin work with Congress and the private sector to prepare for implementing legislation (Continuous).
The Budapest Convention’s Cybercrime Convention Committee is expected to conclude negotiations on a Second Additional Protocol to the treaty in December 2020. The Second Additional Protocol could make several important changes aimed at facilitating more timely and efficient requests for cross-border data in cybercrime and other criminal investigations.256
Given only a limited number of governments can sign CLOUD Act executive agreements, the Second Additional Protocol could be a tremendous incentive for governments to join the Budapest Convention to gain access to the MLA benefits that are being put in place. But strong substantive and procedural protections and civil liberties and human rights safeguards must ensure the Protocol is not misused or abused. The US government should work to conclude negotiations on this Protocol and sign only if such safeguards are adequate in addressing these concerns.257Should the US government expect it will sign the Second Additional Protocol, it should begin briefing and consulting key congressional committees, the private sector, and civil society organizations ahead of time concerning its components and possible domestic legislation to facilitate ratification.
15.4 The Attorney General should direct entities within DOJ to adopt recommendations to make the MLAT system more effective and efficient and ensure the annual budget request reflects the resources needed to implement them (101-180 Days).
Even if more CLOUD Act agreements are signed, its rigorous standards mean agreements are only likely to be entered with a small handful of counties. Thus, the challenges to the MLAT system and cross-border data sharing will likely remain in the long-term. DOS’s “MLAT Reform” project indicates more resources could have an impact on reducing the remaining backlog and streamlining processes.
There are no shortages of worthwhile recommendations to further reform the MLAT system that deserve consideration. These include increasing US government support to programs aimed at building global capacity on cross-border digital evidence requests and US processes,258creating a standardized MLAT request process through electronic forms and online tracking, increasing the number of dedicated personnel working on MLAT requests at OIA, providing OIA with administrative subpoena authority,259and ensuring adequate support for translation of outgoing requests. In all these reforms, DOS must uphold civil liberties protections.260
The Attorney General should direct DOJ entities with assessing the merit and impact of these proposals and direct them to identify the necessary increased resources and legislative changes required to adopt reforms. Any endorsed reforms and budgetary impacts should be integrated into DOJ’s annual budget submission to Congress. Additionally, DOJ, in partnership with DOS, should increase its support for education and training programs for foreign governments on MLA processes.
15.5 DOJ should establish a system to allow for public reporting of MLAT data, including the number of inbound and outbound MLAT requests processed and the average processing time of inbound and outbound requests (181 Days – 1 Year).
No public data currently exists for MLAT requests beyond what has been included in some DOJ Criminal Division budget submissions. However, this data is not standardized across fiscal years, is not always included in every budget request, and contains no granular detail about the scope of governments making such requests and average OIA processing time. This limits transparency for the American public, Members of Congress, and foreign partners wanting to understand the MLAT process. DOS should establish a public reporting system that would be easily accessible to an external audience and request any necessary resources from Congress to implement this system.
15.6 The Attorney General should direct DOJ to provide any necessary additional resources for attaches, legal and cyber advisors, and other personnel placed in foreign missions to meet their mission. DOJ, in cooperation with the FBI and DOS, should evaluate whether decisions are being made as to where to deploy such resources based on a strategic approach and with adequate criteria. DOJ, DOS, and the FBI should work with Congress to authorize and appropriate resources to support increases in personnel as necessary to meet the need (101-180 Days).
DOJ, DOS, FBI, and other government agencies place many personnel in foreign missions to advise on cyber investigations and prosecutions, capacity building, information sharing, MLAs, and other cyber and digital evidence-related priorities.261The US Cyberspace Solarium Commission recommends that Congress authorize and fund an additional 12 FBI ALATs.262This recommendation deserves consideration, but there are many additional forms of personnel the US government places in foreign missions to boost cyber capacity and advise on cybercrime investigations, prosecutions, and extraditions that also deserve consideration for increased support.
DOJ, in coordination with DOS and FBI, should evaluate whether there are currently adequate resources to support the mission of these personnel in advising and boosting the capacity of foreign criminal justice systems to improve cybercrime enforcement. DOJ and DOS should submit to Congress in their annual budget requests a proposal to increase the number of these personnel where necessary to meet the mission and demand. Further, any such budget request increase should also include an evaluation as to how decisions are being made as to where such personnel are deployed, and all future budgets should include data on the number of these personnel deployed overseas and where they are posted.
Monitoring and Measuring Implementation
Objective 16: Establish processes at lead agencies to measure the implementation of all objectives.
16.1 As part of the implementation of each of these recommendations, the lead department or agency for each should establish a process to set a timeline for implementation and a mechanism to monitor implementation and measure impact (Continuous).
Each of the recommendations in this report include a suggested timeframe for implementation. Recognizing there will be many developments that impact these timeframes, the lead departments and agencies for each of these recommendations should establish a process for establishing a realistic timeframe and a mechanism to hold the entities executing them to account for advancing implementation. Additionally, the lead departments and agencies for each of these recommendations should put in place a mechanism that will allow for an assessment on the impact of each of these measures once they are instituted.



