Primer Published September 17, 2020 · 17 minute read
2020 Thematic Brief: US Cybersecurity Efforts
The National Security Program

Takeaways
Cybercrime is exploding. Malicious cyber actions by America’s adversaries are becoming more sophisticated. And cybersecurity remains a top national security issue for the United States. But while we are spending huge amounts of effort to secure our systems, our ability to go after attackers is woefully outdated.
As COVID-19 continues to ravage the globe, malicious actors are exploiting the pandemic and committing cyberattacks for a variety of motives. Nation-states, terrorists, criminal groups, and lone actors have launched cyberattacks and committed cybercrime against large businesses and private citizens, causing devastating impacts to US national and economic security.
While federal, state, and local agencies have taken steps to reduce cyber threats, the Trump Administration has not provided nearly enough resources, does not coordinate efforts, and denies risks posed to election infrastructure.
Here’s what Congress must do:
- Go after the bad actors. We must improve the US government’s capabilities to identify, stop, and punish human cyber attackers in order to close the yawning cyber enforcement gap: the number of cyberattacks launched per year in the United States versus the number of arrests of malicious cyber actors;
- Secure America’s election infrastructure and combat foreign interference and disinformation efforts; and
- Re-establish the United States as a global leader in setting policy around how different actors should behave in cyberspace and boost international cooperation and capacity around these issues.
Cybersecurity remains a top national security issue for the United States, with a wide range of actors posing cyber threats that have economic and national security consequences.
Malicious cyber activity, including cybercrime, has caused devastating impacts to US economic and national security. As Americans increasingly perform more of their daily lives online due to COVID-19, these attacks have only worsened.
A single cyber incident can disrupt thousands of systems worldwide and cost billions of dollars. For example, the NotPetya cyberattack, the most damaging cyberattack in history, caused over $10 billion in damage.1The White House Council of Economic Advisors estimated in 2016 that malicious cyber activity costs the US economy between $57 billion and $109 billion per year.2Other estimates put the number as high as $3 trillion for the global economy annually.3Criminals often perpetrate these attacks for financial gain and target computer networks to conduct data theft, fraud, ransomware, and other illicit activities.4They have also taken advantage of the pandemic, with one estimate showing a 238% rise in cybercrimes against the global financial sector between February and April compared to previous months.5These attacks tend to be perpetrated through “business email compromise” techniques where a criminal sends malware-laced emails to victims; the Federal Bureau of Investigation (FBI) found that these attacks have increased throughout the United States since the pandemic began.6These criminals have also stolen COVID-19 stimulus and unemployment checks from individuals and families, with the US Secret Service noting that $30 billion could be stolen.7Unfortunately, the perpetrators behind these attacks often reside in different countries than the victims, making it very difficult to catch them. Based on Third Way’s analysis, there are only three arrests for every 1,000 malicious incidents.
Beyond financial harm, cyberattacks constitute a serious threat to US national security and public health, which has become amplified during the COVID-19 pandemic. The FBI’s Internet Crime Complaint Center (IC3) received a 400% increase in daily complaints, totaling nearly 4,000, since the pandemic began.8And of particular concern, malicious cyber actors have targeted hospitals treating COVID-19 patients and research institutions working on the developing of COVID-19 vaccines and treatments. In May 2020, US government agencies issued a joint statement with the United Kingdom to warn health care bodies, pharmaceutical companies, universities, and others that nation-state actors could launch cyberattacks against them to steal intellectual property.9Similarly, the FBI and Department of Homeland Security (DHS) issued a warning that the Chinese government is targeting COVID-19 researchers, which could “jeopardize the delivery of secure, effective, and efficient treatment options.”10Indeed, the University of California San Francisco, which was researching for a COVID-19 cure, was hit with a ransomware attack and paid over a million dollars to unlock its data, though the US government has not attributed the attack to China.11The health care industry, though, is just one of several critical infrastructure sectors—such as telecommunications, electrical grids, and dams—that malicious actors target through cyber activity to threaten US national security.12
Even the most essential critical infrastructure to our government, our election system, is not immune from these threats—as Russia’s interference in the 2016 presidential election demonstrates.13Attempts to manipulate our political system through social media have been pervasive and effective. These tactics can be highly effective, and are exacerbated by the fact that over 50% of Americans receive their news from social media14and many have said they have a difficult time discerning the difference between fake and true news.15In fact, misinformation moves six times faster than the truth on Twitter.16
The US intelligence community and the investigation led by Special Counsel Robert Mueller concluded that Russia launched malicious cyber operations to influence the outcome of the 2016 presidential election and help Donald Trump get elected.17The US government indicted at least 26 Russian nationals and three Russian companies for illegally using social media or hacking into computer networks to interfere in the 2016 US election.18Their tactics included stealing data, using fraudulent accounts, staging political rallies, and promoting pro-Trump or anti-Clinton messages through political advertisements.19
Despite these indictments, the Russians were not deterred from trying to interfere in the 2018 midterm elections. Fearing that the Russians would promote damaging fake news on Election Day in 2018, the US military reportedly actively blocked internet access by the Internet Research Agency, the primary Russian entity responsible for creating and disseminating misinformation.20FBI Director Chris Wray would go on to say that Russian interference in the 2018 elections “was at full speed” and a “dress rehearsal for 2020.”21Since then, DHS and the FBI have warned states that the Russians will try to interfere in America’s upcoming elections.22Chinese and Iranian actors have also begun emulating these actions, including reportedly sending virus-laced emails to the Biden and Trump campaigns.23
The Trump Administration’s cybersecurity efforts are underfunded, unmeasurable, and uncoordinated.
While the Trump Administration has taken some steps to expand the US government’s cybersecurity efforts, the agencies responsible for implementing these actions are uncoordinated, have seen their budgets slashed, and lack adequate metrics to determine their effectiveness in reducing the threat.
In the fall of 2018, the White House released the “National Cyber Strategy of the United States,” which detailed how the Administration would create or update policies to combat cyber threats, including cybercrime. This includes participating in global forums to establish international norms and standards, conducting international capacity building efforts to boost the ability of other governments to investigate cybercrime, and hosting gatherings to improve relationships with various law enforcement partners, among other activities.24And in light of the COVID-19 pandemic, federal law enforcement agencies have collaborated with companies to remove hundreds of malicious websites related to COVID-19 scams.25Similarly, federal agencies have created taskforces with Connecticut, Delaware, Virginia, and West Virginia to investigate and prosecute cybercrime related to the pandemic.26
Unfortunately, President Trump eliminated the White House Cyber Coordinator position within the National Security Council (NSC), leaving coordination to two senior director-level NSC officials,27and downgraded the State Department’s Coordinator for Cyber Issues.28The recent US Cyberspace Solarium Commission’s report highlighted this challenge and noted the need for a national cyber director in the White House to coordinate cybersecurity strategy throughout the executive branch—though questions remain about the viability of the proposed structure of this office.29
Further, budgets for federal agencies with cyber enforcement missions have not reflected the increased threat. For example, the White House proposed to reduce the State Department’s International Narcotics and Law Enforcement Bureau’s global capacity building programming for cybercrime and international property rights from $10 million to $5 million the past three years.30Congress rejected these cuts and has thus far appropriated the full $10 million. The National Computer Funding Institute (NCFI), which offers training courses to state and local law enforcement, prosecutors, and judges, also saw a proposed budget cut from $30 million to $4 million for FY2021, significantly below the $35 million needed to operate at full capacity.3132Likewise, the FBI’s National Domestic Communications Assistance Center (NDCAC)—which offers various technical and training assistance to state and locals on digital evidence—had seen their budget decrease 25% over the past eight years while the FBI’s total budget has increased roughly 16% in that same time.33On election security, the Trump Administration and congressional Republicans have stymied efforts to support further funding. While Congress has appropriated over $800 million for election security since 2016,34including an additional $400 million for making them safe as the COVID-19 pandemic continues to spread, this is still well short of the estimated $2 billion needed to adequately secure election infrastructure.35These shortfalls are primarily due to congressional Republicans blocking efforts to provide additional election security funds to state and local governments.36
The Administration’s actions also lack metrics for evaluating their effectiveness in reducing the cyber threat. The National Cyber Strategy does not detail, for example, any framework for monitoring and evaluating the impact of its proposed actions or call for any implementing entities to develop such frameworks. These metrics provide essential information for evaluating how many law enforcement personnel require training to improve response efforts, the impact of indictments and apprehensions on deterring cybercriminals, and the percentage increase in international capacity to combat cybercrime as a result of US programming. While these national strategies tend to be broad and non-prescriptive, strategic implementation plans tend to accompany them to detail these types of metrics and how they should be achieved.37No such implementation plan is known to exist for this strategy.
Congress must hold the Trump Administration accountable for its lack of clarity and consistency in its cyber approach and push for an aggressive and comprehensive cybersecurity strategy for the United States that prioritizes cybercrime enforcement. Congress can consider several pieces of legislation that can achieve this by bolstering resources for cybercrime enforcement training, improving the US government’s capacity to engage in international forums, and securing our elections. For instance, the “Technology in Criminal Justice Act of 2019” (H.R.5227) would distribute and expand grants for institutions to train federal, state, and local law enforcement personnel in digital evidence activities, among other things.38And the “Cyber Diplomacy Act of 2019” (H.R. 739) would enable the United States to more fully engage in the international arena related to cybersecurity by creating an Office of International Cyberspace Policy in the State Department.39Lastly, Members of Congress should continue to advocate for increased funding for state and local governments to secure their election infrastructure, such as in future COVID-19 stimulus packages like “The Heroes Act” (H.R. 6800).40
Congress must now take action to strengthen the US government’s efforts to combat malicious cyber activity.
To strengthen the US government’s efforts to combat malicious cyber activity and create coherence and effectiveness in the government’s approach, Congress must act now to:
1. Improve the US government’s capabilities to identify, stop, and punish human cyber attackers to close the cyber enforcement gap.
The United States requires a rebalance in its cybersecurity policies: from a heavy focus on building better cyber defenses against intrusion to waging a more robust effort to prosecute human attackers. Achieving this would require a more balanced approach that places greater emphasis on law enforcement and diplomacy. Congress can stop the cybercrime wave and close the cyber enforcement gap by transforming law enforcement, enabled by diplomacy and international capacity building, to punish and hold accountable human beings perpetrating or ordering attacks.
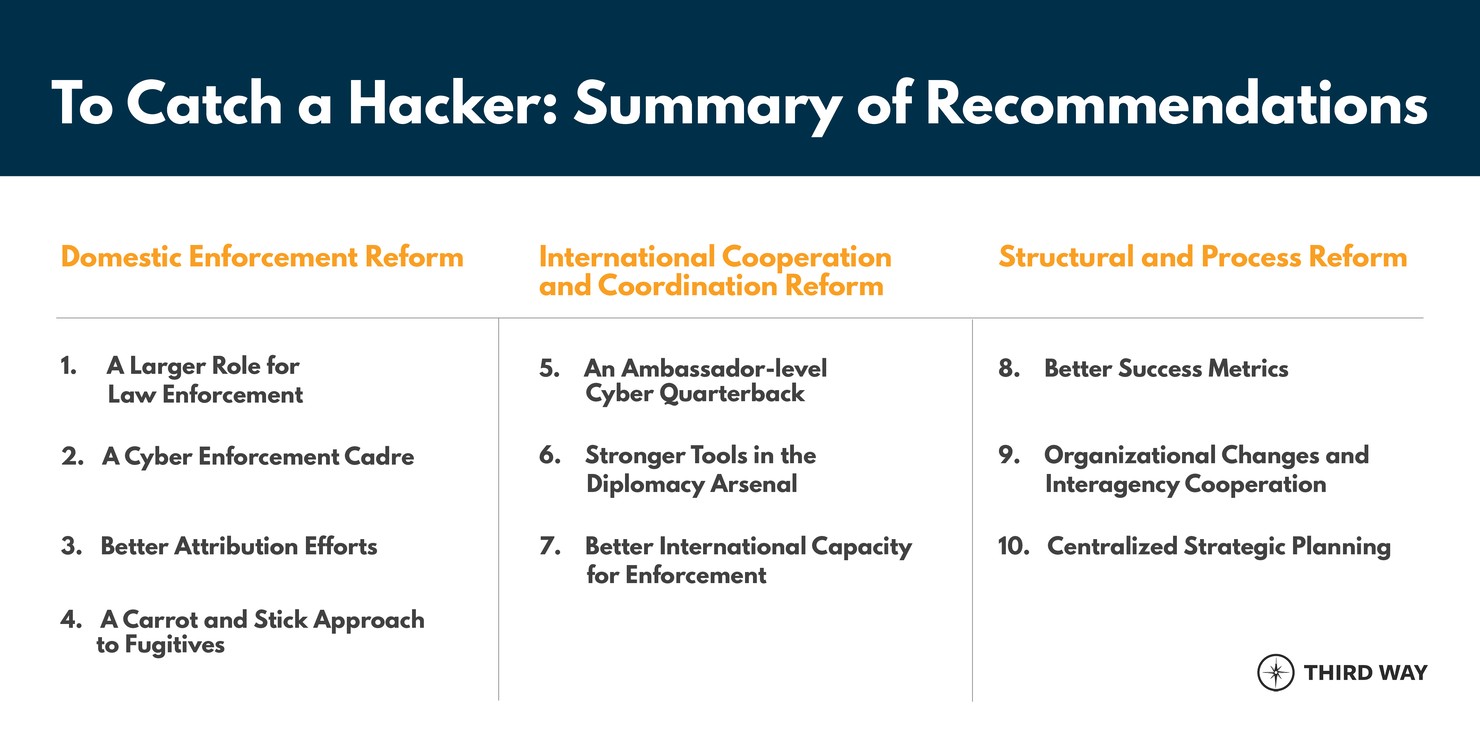
Third Way established 10 policy areas that require urgent attention from Congress to reduce the cyber enforcement gap:
As a first step, Congress must work to establish a baseline to understand the scope of the cyber enforcement problem. This will lay the foundation for a comprehensive strategy aimed at closing the cyber enforcement gap. A comprehensive assessment of current government efforts across all agencies with a role in cyber enforcement is required to determine what works, what might need to be amplified, and what might need to change. Establishing a baseline would include requiring a government-wide assessment of the current levels of US law enforcement actions,41as well as an analysis of the amount and effectiveness of support provided to other countries by the US State Department to build their capacity around cyber investigations.42Without baseline statistics, Congress will face difficulties in measuring government efforts and making an informed case for budget increases necessary to support increased enforcement levels. Congress can address this by mandating these baseline assessments and pushing for cyber enforcement agencies to establish better metrics to measure the extent of the problem.43
Second, despite the lack of metrics, Congress can question the Trump Administration’s proposed budget cuts to cyber initiatives and evaluate whether agencies have sufficient funds to fulfill their roles and responsibilities. In annual appropriations bills, Members of Congress may want to identify areas in the Administration’s National Cyber Strategy where further resources may be needed to implement the actions. And to ensure the Administration spends funds efficiently, Congress can conduct oversight on how cybercrime enforcement policies are coordinated and evaluated across departments and agencies. The answers to these questions are imperative as cybercrime continues to rise during the COVID-19 pandemic and the need for interagency, private, and international partnerships to stop criminals is becoming increasingly paramount.44
2. Invest in securing America’s election infrastructure and combating foreign interference and disinformation efforts.
As US adversaries continue to launch various cyber tactics against US democratic processes and institutions, Congress needs to invest in securing America’s election infrastructure, ensuring campaigns do not receive foreign assistance, and combating disinformation efforts at all costs.
First, Congress should appropriate sufficient funding to state and local governments to adequately protect their election infrastructure from cybersecurity threats leading up to the 2020 elections and beyond. While election security experts have identified measures to enhance the cybersecurity of election infrastructure—such as voter registration databases, voting machines, and reporting systems—state and local governments lack the funds necessary to fully implement these measures. Security officials agree that local jurisdictions need voter-verified paper audit trails, risk-limiting audits, paper ballots, and additional tried and tested security measures to enhance their security postures.45Unfortunately, only half of the states with paperless voting machines in 2016 will have replaced them by the 2020 elections, meaning that 12% of voters will vote on paperless equipment in 2020.46Further, 26 states do not require post-election audits.47As a result, election officials may struggle in verifying voters’ ballots in the wake of any actual or perceived interference. Fortunately, House Democrats passed the Heroes Act (H.R. 6800) in May 2020, which would allocate over $3.5 billion to minimize COVID-19 risks to voters and enhance voter security.48As the elections loom, it will be increasingly difficult for election officials to implement these security measures. Nonetheless, Congress should continue to advocate for additional spending for measures that can be implemented immediately and ensure funding is sustained over several years.
Second, Congress should consider legislative proposals to mitigate the impact of foreign actors meddling in the elections by reducing their ability to offer assistance to candidates and campaigns. Just as the Russians hacked Hilary Clinton’s campaign and various Democratic Party organizations to support Donald Trump in 2016,49the FBI and DHS have warned that they are expected to perform similar tactics in 2020. But Republicans have resisted efforts to mitigate this threat.50The Democratic Congressional Campaign Committee (DCCC) has twice requested that the National Republican Congressional Committee (NRCC) not use hacked materials in the 2020 elections. The NRCC has denied the requests both times.51Congress should consider legislative proposals that would require presidential campaigns to report foreign contacts and assistance before the elections.52Additionally, Congress should consider further actions to protect America’s elections from foreign interference and discourage the use of hacked materials, such as establishing norms on how the media handles stolen information, mandating transparency in the use of foreign consultants and companies in campaigns, and increasing transparency concerning candidate’s foreign business interests.53
Lastly, Congress must work to combat foreign disinformation campaigns aimed at sowing division among the American public and injecting doubts in voters’ minds about the democratic process. The Russians have begun instituting lessons learned from their 2016 experience to be more effective in disseminating disinformation in the 2020 election. Congress must educate the public about disinformation efforts by Russia and other governments and condemn President Trump’s attempts to ignore or downplay them. Congress must also collaborate with technology companies to shore up their defenses against foreign influence operations and protect against the spread of disinformation.54
3. Re-establish the United States as a global leader in setting policies on behavior in cyberspace and boost international cooperation and capacity on this issue.
The global nature of the cyber threat requires dedicated and deliberate leadership and coordination at the highest echelons of the US government. Given the scope of countries impacted by cyber threats, little progress can be made in America’s cybersecurity efforts if our cyber diplomatic and development efforts are not expanded and strengthened. To catch international cybercriminals, America needs a coordinated international effort and cooperation on cyber investigations.
Legislation such as the “Cyber Diplomacy Act of 2019” (H.R. 739) to elevate the Office of the Coordinator for Cyber Issues at the State Department is a critical first step, but is not enough.55The office must also receive a clear mandate that includes a focus on closing the cybercrime enforcement gap, strengthening its efforts to identify the perpetrators of cyberattacks, and implementing diplomatic training programs. Congress must also provide it with the necessary resources and personnel to implement those initiatives. Positioning and equipping the State Department as a key entity on the global stage is critical to drive forward a rebalance in America’s cybersecurity approach.
Congress must also continue to encourage strong US leadership in international forums aimed at establishing norms guiding the behavior of nations in cyberspace and push for the US government itself to abide by any agreed upon norms. The development of new, and strengthening of existing, global cyber norms was a component of the US International Cyberspace Policy articulated in the “Cyber Diplomacy Act” and was also highlighted in the final report of the US Cyberspace Solarium Commission.56Members of Congress have also directly called on the State Department to step up its leadership in this area.57 While the Trump Administration continues to undermine these efforts by disengaging and pulling funds from international organizations and forums and eliminating the position of America’s top cyber diplomat, Congress must step in and promote US leadership in these efforts and ensure these entities have adequate resources to continue their missions.58
Lastly, Congress must provide adequate resources to global cyber capacity building efforts and push for more accountability in how these resources are being spent. The US government, primarily through the Departments of State and Justice, provides support to programs aimed at building the capacity of priority foreign governments on a wide range of cybersecurity issues. This includes providing support to programs aimed at strengthening the capability of criminal justice sectors in other countries to investigate and prosecute cybercrime. Yet, it is unclear how much the US government is spending on these efforts and what metrics are being used to monitor their impact, guide decisions on where and when resources are being deployed, and ensure adequate human rights safeguards are in place to prevent misuse or abuse. And funding for these efforts pales in comparison to the capacity building support provided by the US government to deal with other global threats such as terrorism. Congress can continue to push for such evaluations and ensure through annual appropriations bills that adequate resources are provided to these global cyber capacity building efforts commensurate to the threat.59
Conclusion
As the COVID-19 virus continues to devastate the United States, malicious cyber actors will continue to exploit the pandemic for their own gain. While the executive branch has taken a number of actions to impose consequences on the perpetrators of this cyber activity, the Trump Administration’s approach to this threat remains incoherent and inadequate, starting with the President’s refusal to acknowledge Russia’s attempt to influence the 2016 presidential elections. The Administration has eliminated critical cyber positions from the White House and the State Department, undoing the progress made in previous administrations. Congressional Republicans, along with the White House, have also impeded substantial investment to secure our elections.
Congress has an opportunity to assert its authority and act in our national security interest by taking actions in a number of areas, including: 1) improving the US government’s capability to identify, stop, and punish malicious cyber actors; 2) investing in election security and combatting foreign influence operations; and 3) re-establishing the US as a global leader in cyberspace.

